How to Set Up Remote Access to Your Computer From Anywhere
In today's interconnected world, the ability to access your computer from anywhere has transformed from a luxury convenience into an essential necessity. Whether you're a business professional needing to retrieve critical files from your office computer while traveling, a student accessing research materials from your dorm room computer, or a tech enthusiast managing multiple systems across different locations, remote access technology has become the backbone of modern digital flexibility. This comprehensive guide will walk you through the intricacies of setting up secure, reliable remote access to your computer from virtually anywhere in the world. We'll explore various methods ranging from built-in operating system solutions to third-party applications, examine security considerations that protect your data and privacy, and provide step-by-step instructions for implementing these solutions effectively. By understanding the fundamental principles, security protocols, and practical applications of remote access technology, you'll be equipped to make informed decisions about which approach best suits your specific needs while maintaining the highest standards of digital security and performance optimization.
1. Understanding Remote Access Fundamentals

Remote access technology operates on the principle of establishing a secure connection between two computers over a network, typically the internet, allowing one device to control another as if the user were physically present at the remote machine. This connection relies on specialized protocols and software that transmit screen images, keyboard inputs, and mouse movements between the local and remote computers in real-time. The fundamental architecture involves a host computer (the one being accessed remotely) running server software that listens for incoming connections, and a client computer (the one initiating the connection) running client software that establishes and maintains the communication link. Understanding this basic client-server relationship is crucial because it determines how you'll configure your network settings, security permissions, and software installations. The quality of your remote access experience depends heavily on factors such as internet bandwidth, network latency, the processing power of both computers, and the efficiency of the remote access software being used. Modern remote access solutions employ various optimization techniques including data compression, adaptive quality adjustment, and intelligent bandwidth management to ensure smooth performance even over slower internet connections.
2. Built-in Operating System Solutions

Most modern operating systems include native remote access capabilities that provide a solid foundation for basic remote connectivity needs without requiring additional software installations. Windows computers feature Remote Desktop Protocol (RDP), a robust built-in solution that offers excellent performance and integration with Windows security features, allowing users to access their desktop environment with full functionality including file transfers, printer access, and multi-monitor support. Mac users can leverage Screen Sharing through the built-in VNC (Virtual Network Computing) server, which integrates seamlessly with macOS security settings and provides reliable access to the desktop environment with support for various authentication methods. Linux distributions typically include VNC servers and SSH capabilities that can be configured for both command-line and graphical remote access, offering flexibility for different user preferences and technical requirements. These built-in solutions offer several advantages including deep integration with the operating system's security framework, no additional licensing costs, and regular security updates through the standard OS update process. However, they may have limitations in terms of advanced features, cross-platform compatibility, and ease of setup for non-technical users, which is where third-party solutions often provide additional value and functionality.
3. Third-Party Remote Access Software

The market for third-party remote access software offers a diverse range of solutions designed to address various user needs, from simple personal use to enterprise-level deployments with advanced security and management features. Popular commercial solutions like TeamViewer, LogMeIn, and AnyDesk provide user-friendly interfaces, cross-platform compatibility, and advanced features such as file transfer capabilities, session recording, multi-monitor support, and mobile device integration. These platforms typically offer both free versions for personal use and paid subscriptions for commercial applications, with the paid versions including additional features like unattended access, priority support, and enhanced security options. Open-source alternatives such as TightVNC, UltraVNC, and Chrome Remote Desktop provide cost-effective solutions with customizable features, though they may require more technical expertise to configure and maintain properly. When evaluating third-party solutions, consider factors such as ease of installation and configuration, cross-platform compatibility requirements, security features including encryption standards and authentication methods, performance optimization capabilities, and the total cost of ownership including licensing fees and support costs. Many of these solutions also offer cloud-based connectivity that simplifies network configuration by eliminating the need for complex firewall and router settings, making them particularly attractive for users who lack advanced networking knowledge.
4. Network Configuration and Port Forwarding

Proper network configuration forms the foundation of successful remote access implementation, requiring careful attention to router settings, firewall configurations, and port forwarding rules that enable external connections while maintaining security. Port forwarding involves configuring your router to direct incoming traffic on specific ports to the appropriate computer on your local network, essentially creating a pathway through your network's protective barriers for legitimate remote access attempts. For Windows Remote Desktop, you'll typically need to forward port 3389, while VNC connections usually require port 5900, though these default ports should be changed to non-standard numbers to enhance security against automated attacks. The process involves accessing your router's administrative interface, locating the port forwarding or virtual server settings, and creating rules that map external ports to internal IP addresses and ports on your target computer. Dynamic DNS services become crucial when your internet service provider assigns dynamic IP addresses that change periodically, as these services provide a consistent domain name that automatically updates to reflect your current IP address. Additionally, configuring your computer's local firewall to allow remote access connections while blocking unauthorized traffic requires careful balance between accessibility and security, often involving the creation of specific firewall rules that permit connections only on designated ports and from trusted sources.
5. Security Considerations and Best Practices

Security represents the most critical aspect of remote access implementation, as improperly configured systems can become vulnerable to unauthorized access, data theft, and malicious attacks that compromise both personal and professional information. Strong authentication mechanisms form the first line of defense, requiring the implementation of complex passwords, two-factor authentication where available, and regular password updates to prevent unauthorized access attempts. Network-level security measures include changing default ports to non-standard numbers, implementing IP address restrictions that limit connections to specific geographic regions or known IP ranges, and using VPN connections to encrypt all traffic between the client and host computers. Regular security audits should include monitoring access logs for suspicious activity, keeping remote access software updated with the latest security patches, and configuring automatic screen locks and session timeouts to prevent unauthorized access if a remote session is left unattended. Advanced security practices involve implementing certificate-based authentication, using dedicated user accounts with limited privileges for remote access purposes, and employing network segmentation to isolate remote-accessible computers from sensitive network resources. Consider implementing additional security layers such as intrusion detection systems, regular security scans, and backup procedures that protect against both accidental data loss and malicious attacks that might target remotely accessible systems.
6. Mobile Device Integration

Modern remote access solutions increasingly emphasize mobile device compatibility, recognizing that smartphones and tablets have become primary computing devices for many users who need flexible access to their desktop computers while traveling or working remotely. Mobile applications for remote access typically provide optimized interfaces that adapt desktop environments to smaller touchscreens, implementing gesture-based controls, virtual keyboards, and simplified navigation methods that make desktop interaction practical on mobile devices. iOS and Android applications from major remote access providers offer features such as file browsing and transfer, clipboard synchronization, and the ability to wake sleeping computers remotely, transforming mobile devices into powerful remote computing tools. The technical challenges of mobile remote access include managing varying network conditions as devices switch between WiFi and cellular connections, optimizing data usage to prevent excessive cellular charges, and adapting desktop interfaces designed for mouse and keyboard interaction to touch-based input methods. Performance optimization for mobile devices involves implementing adaptive streaming technologies that adjust image quality and frame rates based on available bandwidth and device capabilities, ensuring usable performance even over slower cellular connections. Security considerations for mobile remote access include implementing device-specific authentication methods such as biometric login, secure storage of connection credentials, and automatic session termination when applications are backgrounded or devices are locked.
7. Performance Optimization Techniques
Optimizing remote access performance requires understanding the various factors that affect connection quality and implementing strategies to maximize responsiveness while minimizing bandwidth consumption and system resource usage. Network optimization begins with ensuring adequate bandwidth on both ends of the connection, as remote access performance is fundamentally limited by the slowest network link in the connection path, whether that's the upload speed from the host location or download speed at the client location. Quality of service (QoS) configuration on network equipment can prioritize remote access traffic over less critical applications, reducing latency and improving responsiveness during periods of high network utilization. Software-level optimizations include adjusting color depth and screen resolution settings to reduce data transmission requirements, disabling visual effects and animations that consume bandwidth without adding functional value, and configuring compression algorithms that balance image quality against transmission speed. Advanced optimization techniques involve implementing caching mechanisms that store frequently accessed screen elements locally, using differential compression that transmits only changed portions of the screen, and employing adaptive algorithms that automatically adjust quality settings based on real-time network performance measurements. Hardware considerations include ensuring adequate processing power and memory on both computers, using wired network connections where possible to reduce latency and improve reliability, and implementing dedicated network interfaces for remote access traffic in high-performance environments.
8. Troubleshooting Common Connection Issues
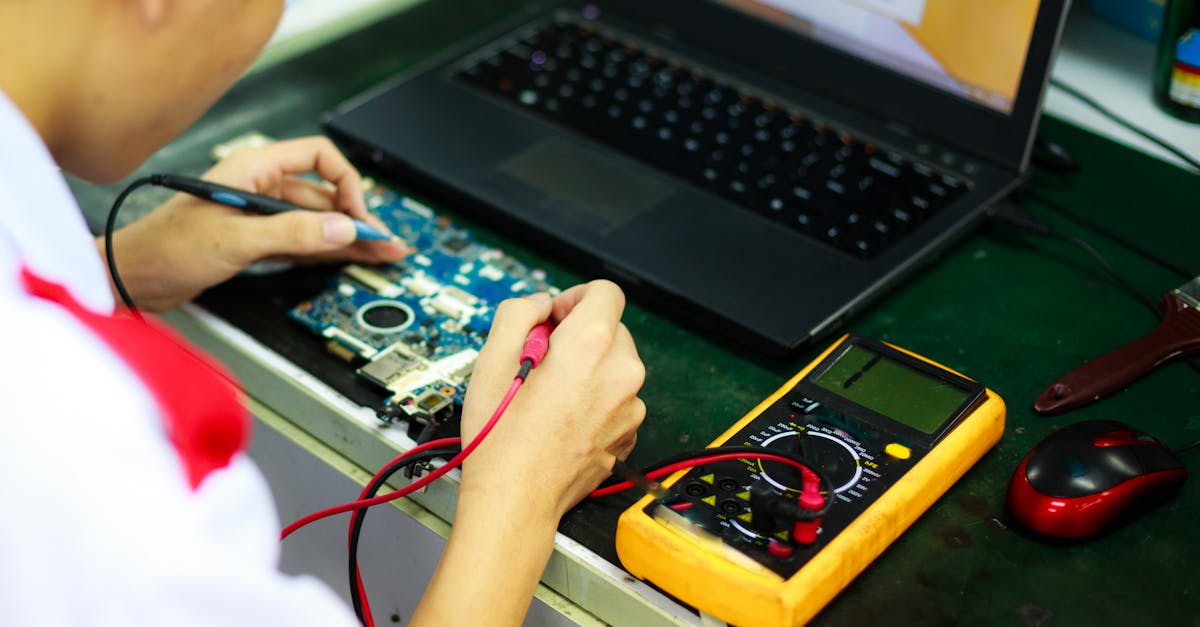
Remote access implementations frequently encounter connectivity problems that require systematic troubleshooting approaches to identify and resolve underlying issues affecting connection establishment and performance. Connection failures often stem from network configuration problems including incorrect port forwarding settings, firewall rules blocking necessary traffic, or dynamic IP address changes that invalidate saved connection settings. Systematic troubleshooting begins with verifying basic network connectivity using tools like ping and traceroute to ensure the target computer is reachable over the network, followed by testing specific port accessibility using port scanning tools or telnet connections. Authentication failures typically indicate problems with user credentials, account permissions, or security policy conflicts that prevent successful login attempts, requiring verification of username and password combinations, account status, and group membership settings. Performance issues such as slow response times, choppy video, or frequent disconnections often result from bandwidth limitations, network congestion, or suboptimal software configuration settings that can be addressed through quality adjustments, compression optimization, or network infrastructure improvements. Advanced troubleshooting techniques include analyzing network packet captures to identify protocol-level issues, reviewing system logs for error messages and security events, and using network monitoring tools to identify bandwidth bottlenecks or latency problems that affect connection quality. Documentation of troubleshooting steps and solutions creates valuable knowledge bases for resolving similar issues in the future and helps identify patterns that might indicate systemic problems requiring infrastructure improvements.
9. Advanced Features and Automation

Modern remote access solutions offer sophisticated features that extend beyond basic screen sharing to provide comprehensive remote computing capabilities including automated maintenance, scheduled access, and integration with other business systems. Unattended access capabilities allow remote connections to computers without requiring physical presence at the host machine, enabling automated system maintenance, remote troubleshooting, and scheduled file transfers that operate outside normal business hours. Wake-on-LAN functionality enables remote activation of powered-down computers over the network, providing energy-efficient remote access that allows systems to remain in low-power states until needed for remote sessions. File transfer and synchronization features provide secure methods for moving data between local and remote computers, often including resume capabilities for interrupted transfers and bandwidth throttling to prevent network congestion. Session recording and audit capabilities create detailed logs of remote access activities for security compliance and troubleshooting purposes, capturing screen activity, file transfers, and system changes made during remote sessions. Integration with directory services such as Active Directory enables centralized user management and single sign-on capabilities that simplify administration in enterprise environments. Advanced automation features include scripting capabilities that automate repetitive tasks, scheduled maintenance windows that perform system updates and backups remotely, and integration with monitoring systems that trigger remote access sessions in response to system alerts or performance issues.
10. Future Trends and Emerging Technologies

The evolution of remote access technology continues to accelerate, driven by changing work patterns, advancing hardware capabilities, and emerging security requirements that shape the development of next-generation remote computing solutions. Cloud-based remote access platforms are increasingly replacing traditional peer-to-peer connections with scalable, managed services that provide enhanced security, simplified configuration, and improved performance through global infrastructure optimization. Artificial intelligence and machine learning technologies are being integrated into remote access solutions to provide predictive performance optimization, automated security threat detection, and intelligent bandwidth management that adapts to usage patterns and network conditions. Virtual and augmented reality technologies promise to transform remote access experiences by providing immersive interfaces that make remote interaction more natural and intuitive, potentially replacing traditional screen sharing with three-dimensional computing environments. Zero-trust security models are influencing remote access design by implementing continuous authentication and authorization processes that verify user identity and device security status throughout remote sessions rather than relying solely on initial login credentials. Edge computing technologies are enabling distributed remote access infrastructure that reduces latency and improves performance by processing remote access traffic closer to end users, while quantum computing developments may eventually revolutionize encryption and security protocols used in remote access systems. The integration of Internet of Things (IoT) devices and smart home technologies with remote access systems is creating new possibilities for comprehensive remote environment management that extends beyond traditional computing devices to include environmental controls, security systems, and other connected devices.