The Reason Copy-Paste Fails Between Apps — and the Workaround
In the digital age, copy-paste functionality has become as fundamental to our computing experience as breathing is to life itself. Yet, despite its apparent simplicity, this seemingly universal feature often fails us at the most critical moments, leaving users staring at blank paste operations or garbled text transfers between applications. The frustration is palpable when you meticulously format a document in one application, only to watch it transform into plain text chaos when pasted into another. This phenomenon isn't merely a minor inconvenience—it represents a complex interplay of operating system architectures, application programming interfaces, security protocols, and data format incompatibilities that have evolved over decades of software development. Understanding why copy-paste fails between apps requires delving into the intricate mechanisms that govern data transfer in modern computing environments, from clipboard management systems to sandboxing restrictions that prioritize security over convenience. This comprehensive exploration will uncover the technical foundations behind these failures and, more importantly, provide practical workarounds that can restore seamless data transfer across your digital workflow.
1. The Architecture of Clipboard Systems - Understanding the Foundation
The clipboard system serves as the invisible bridge between applications, operating as a temporary storage mechanism that holds copied data until it's pasted elsewhere. At its core, the clipboard functions through a sophisticated architecture that varies significantly across operating systems, with Windows utilizing a centralized clipboard service, macOS employing a pasteboard server, and Linux distributions implementing various clipboard managers through X11 or Wayland protocols. This architectural diversity creates the first layer of complexity in cross-application data transfer. When you copy content, the source application doesn't simply store raw text or images; instead, it registers multiple data formats simultaneously—plain text, rich text, HTML, proprietary formats, and metadata—creating what developers call a "clipboard flavor list." The receiving application must then negotiate which format it can best interpret and display. However, this negotiation process is where many failures originate, as applications may prioritize different formats or lack support for the specific data types being transferred. Modern operating systems have attempted to standardize these interactions through APIs like Windows' Clipboard API or macOS's NSPasteboard, but legacy applications, security restrictions, and proprietary formats continue to create friction in what should be a seamless process.
2. Security Sandboxing - The Double-Edged Sword of Protection

Modern operating systems have implemented increasingly sophisticated security measures that, while protecting users from malicious software, inadvertently create barriers to clipboard functionality. Application sandboxing, a cornerstone of contemporary security architecture, isolates programs within restricted environments that limit their access to system resources, including the clipboard. This isolation prevents malicious applications from stealing sensitive data that users might copy, such as passwords, financial information, or personal documents. However, these same protective measures can interfere with legitimate clipboard operations, particularly when transferring data between applications with different security privileges or trust levels. Mobile operating systems like iOS and Android have particularly strict clipboard access controls, requiring explicit permissions and often clearing clipboard contents after predetermined time intervals. Enterprise environments compound these challenges by implementing additional security policies that may restrict clipboard access entirely or filter content based on data loss prevention protocols. The result is a delicate balance between security and functionality, where overly restrictive policies can render copy-paste operations unreliable or completely non-functional. Understanding these security implications is crucial for users who need to maintain both data protection and operational efficiency in their daily workflows.
3. Format Incompatibilities - When Data Speaks Different Languages

One of the most common reasons for copy-paste failures lies in the fundamental incompatibility between data formats used by different applications. Each software program interprets and stores information according to its own internal logic and requirements, creating a digital Tower of Babel where applications literally speak different languages. When copying formatted text from a word processor like Microsoft Word, the application embeds extensive formatting information including font families, sizes, colors, paragraph styles, and embedded objects. However, when pasting into a simple text editor or web form, these rich formatting elements become incompatible noise that either gets stripped away or causes the paste operation to fail entirely. Similarly, spreadsheet applications like Excel store data with complex metadata including formulas, cell references, and formatting rules that have no equivalent in standard text applications. Vector graphics copied from design software contain mathematical descriptions of shapes and curves that cannot be interpreted by applications expecting bitmap images. Even seemingly simple operations like copying a file path from a file manager to a command-line interface can fail due to character encoding differences, path separator conventions, or special character handling. These format incompatibilities represent more than mere technical limitations—they reflect the diverse and specialized nature of modern software applications, each optimized for specific tasks and data types.
4. Memory Management and Timing Issues - The Race Against Time
The temporal nature of clipboard operations introduces another layer of complexity that frequently leads to copy-paste failures. Unlike permanent file storage, clipboard data exists in volatile memory with limited lifespans and specific timing requirements that can cause operations to fail if not executed within narrow windows. When an application copies data to the clipboard, it doesn't necessarily transfer the actual content immediately; instead, it may register a promise to provide the data when requested, a mechanism known as "lazy loading" or "deferred rendering." This approach conserves memory and improves performance for large data sets, but it creates vulnerabilities when the source application closes, crashes, or becomes unresponsive before the paste operation occurs. Memory pressure on the system can also cause clipboard contents to be purged prematurely, particularly on mobile devices with limited RAM or when multiple applications compete for resources. Additionally, some applications implement their own clipboard timeout mechanisms, automatically clearing copied content after predetermined intervals for security reasons. The asynchronous nature of modern computing further complicates timing issues, as background processes, system updates, or resource-intensive operations can interrupt the delicate handshake between copying and pasting applications. These timing-related failures often appear random to users, occurring inconsistently and making troubleshooting particularly challenging.
5. Cross-Platform Challenges - Bridging Different Worlds

The modern computing landscape encompasses multiple operating systems, each with distinct clipboard implementations that create significant challenges for users working across platforms. Windows, macOS, and Linux handle clipboard operations through fundamentally different mechanisms, with varying support for data formats, security models, and inter-application communication protocols. When using remote desktop solutions, virtual machines, or cloud-based applications, these platform differences become magnified, often resulting in complete clipboard isolation or severely limited functionality. Web applications introduce additional complexity by operating within browser sandboxes that implement their own clipboard APIs, which may not align with native operating system capabilities. The HTML5 Clipboard API, while standardizing some web-based copy-paste operations, still faces browser compatibility issues and security restrictions that can prevent seamless data transfer. Mobile platforms present perhaps the greatest cross-platform challenges, with iOS and Android implementing strict clipboard access controls that frequently conflict with desktop application expectations. Cloud synchronization services attempt to bridge these gaps by providing clipboard sharing across devices, but they introduce latency, security concerns, and dependency on network connectivity. Enterprise environments often compound cross-platform issues by implementing different security policies and software versions across various systems, creating a patchwork of compatibility challenges that can make simple copy-paste operations unpredictable and unreliable.
6. Application-Specific Limitations - When Software Plays Defense

Individual applications often implement their own restrictions and limitations that can interfere with standard clipboard operations, sometimes by design and other times as unintended consequences of specific programming choices. Many applications, particularly those handling sensitive information like password managers or financial software, deliberately restrict clipboard access to prevent data theft or accidental exposure. These applications may clear clipboard contents immediately after pasting, implement one-time use policies, or encrypt clipboard data in ways that make it inaccessible to other programs. Content management systems and digital rights management (DRM) protected applications frequently disable copy functionality entirely to prevent unauthorized distribution of copyrighted material. Web browsers implement varying levels of clipboard access based on security policies, user permissions, and the specific context of the web page, often requiring explicit user interaction or permission grants for clipboard operations. Legacy applications present unique challenges, as they may have been developed before modern clipboard standards were established, resulting in incompatible or limited clipboard implementations. Some applications use proprietary clipboard formats that can only be interpreted by other software from the same vendor, creating artificial barriers to data portability. Additionally, applications running with elevated privileges may be unable to exchange clipboard data with standard user-level programs due to security isolation measures, creating unexpected barriers in seemingly straightforward workflows.
7. Network and Cloud-Based Complications - When Distance Matters

The increasing prevalence of cloud-based applications and remote computing solutions has introduced network-related complications that can significantly impact clipboard functionality. When working with web applications, Software-as-a-Service (SaaS) platforms, or remote desktop environments, clipboard operations must traverse network connections that introduce latency, bandwidth limitations, and potential points of failure. Cloud-based office suites like Google Workspace or Microsoft 365 online versions often implement their own clipboard mechanisms that may not integrate seamlessly with local applications, creating data silos that prevent smooth workflow transitions. Remote desktop protocols like RDP, VNC, or proprietary solutions each handle clipboard redirection differently, with varying levels of format support and security restrictions that can cause copy-paste operations to fail or behave unexpectedly. Virtual private networks (VPNs) and corporate firewalls may block or filter clipboard data transfers as part of data loss prevention strategies, particularly when copying sensitive information between internal and external applications. Network interruptions, server downtime, or synchronization delays can cause clipboard contents to become stale or inaccessible, leaving users with failed paste operations and no clear indication of the underlying cause. Additionally, browser-based applications must navigate complex security policies that may prevent clipboard access entirely or require explicit user permissions for each operation, creating friction in what should be seamless data transfer processes.
8. The Hidden Role of Character Encoding and Localization
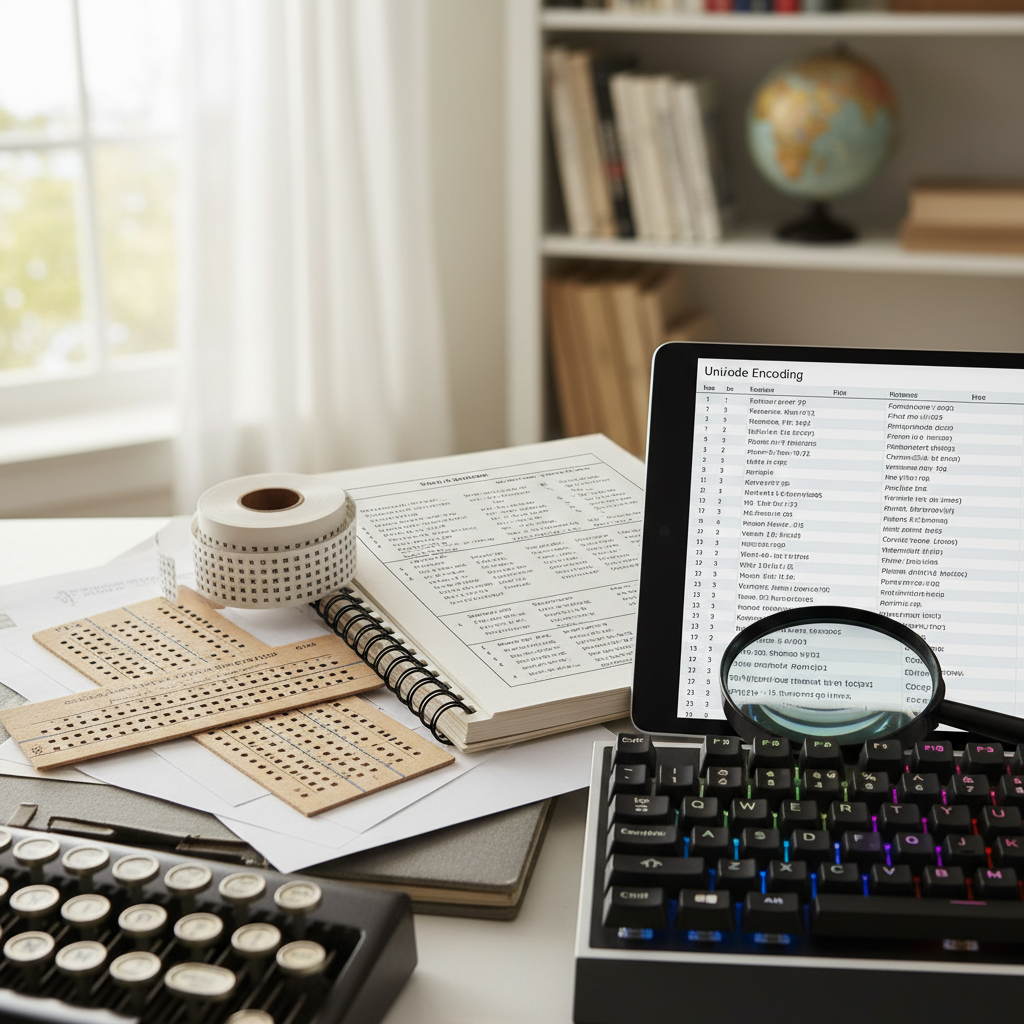
Character encoding represents one of the most subtle yet persistent causes of copy-paste failures, particularly when transferring text between applications with different language support or regional settings. The evolution from ASCII to Unicode has created a complex landscape of character encoding standards including UTF-8, UTF-16, Windows-1252, and numerous legacy encodings that can cause text to become corrupted or completely unreadable during clipboard transfers. When copying text containing special characters, accented letters, or non-Latin scripts, the source and destination applications must agree on the appropriate encoding scheme, a negotiation that frequently fails silently. This issue becomes particularly problematic when working with applications developed in different regions or time periods, as they may default to incompatible character sets. Localization settings further complicate matters, as applications may interpret clipboard data differently based on system locale, date formats, number representations, and currency symbols. Right-to-left languages like Arabic or Hebrew introduce additional complexity, as the directional formatting information may not transfer correctly between applications, resulting in scrambled or reversed text. Even seemingly simple operations like copying file paths can fail when directory names contain international characters that aren't properly encoded or decoded during the clipboard transfer. These encoding issues often manifest as mysterious question marks, boxes, or completely garbled text, leaving users puzzled about why their copy-paste operation produced unintelligible results.
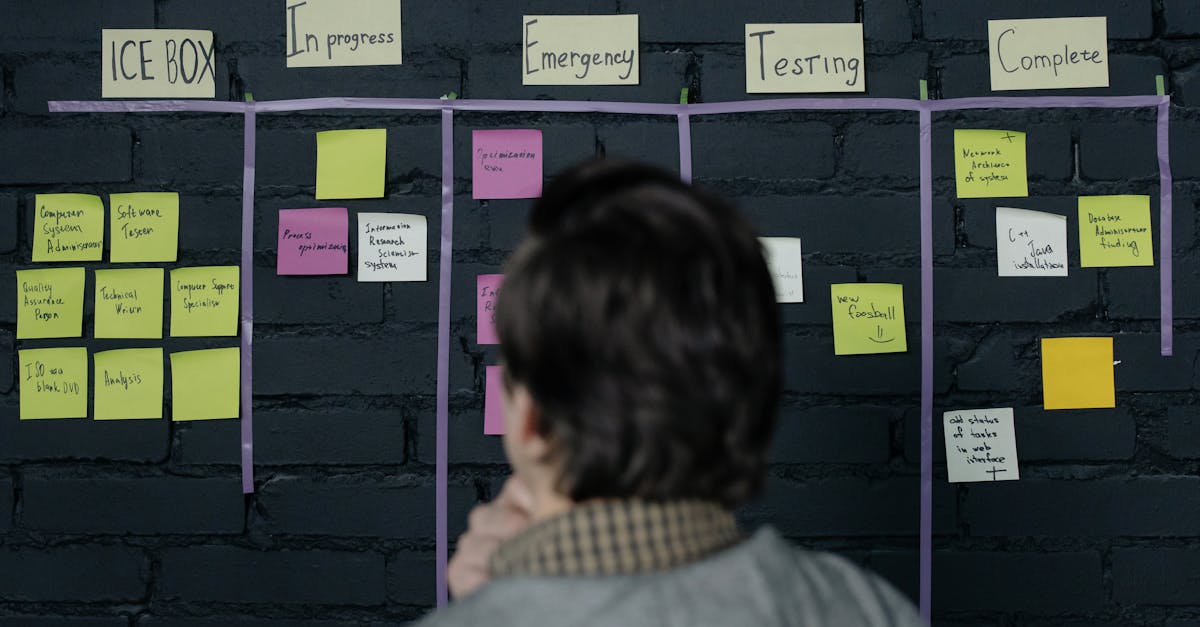
9. Comprehensive Workaround Strategies - Practical Solutions for Every Scenario

Despite the numerous technical challenges that can cause copy-paste failures, a variety of practical workarounds can restore functionality and improve reliability across different scenarios. For format compatibility issues, intermediate applications like plain text editors can serve as neutral ground, stripping problematic formatting while preserving essential content that can then be copied to the final destination. Specialized clipboard managers such as ClipX, Ditto, or macOS's built-in clipboard history provide enhanced functionality including format conversion, persistent storage, and cross-application compatibility improvements. When dealing with security restrictions, temporarily adjusting application permissions or using trusted intermediary applications can bypass sandboxing limitations, though users must balance convenience with security considerations. For cross-platform scenarios, cloud-based clipboard synchronization services like Pushbullet, Microsoft's Cloud Clipboard, or Apple's Universal Clipboard can bridge the gap between different operating systems and devices. Browser extensions and web-based tools can facilitate clipboard operations in web applications where native functionality is restricted. When character encoding issues arise, specialized text conversion utilities can translate between different encoding schemes, ensuring proper character representation across applications. For enterprise environments with strict security policies, working with IT administrators to configure appropriate exceptions or using approved data transfer methods can maintain both security and productivity. Additionally, understanding application-specific keyboard shortcuts, export/import functions, and alternative data transfer methods can provide backup options when traditional copy-paste operations fail.
10. Future-Proofing Your Workflow - Adapting to an Evolving Landscape
The future of clipboard functionality will likely be shaped by evolving security requirements, cross-platform integration demands, and emerging technologies that promise both new capabilities and fresh challenges. As artificial intelligence becomes more integrated into operating systems and applications, we can expect smarter clipboard managers that automatically detect and convert between incompatible formats, predict user intentions, and provide contextual suggestions for data transfer operations. However, these advances will likely come with increased privacy concerns and security restrictions that may further complicate traditional copy-paste workflows. To future-proof your data transfer processes, consider adopting flexible strategies that don't rely solely on clipboard functionality, such as cloud-based document collaboration, API-based integrations, and standardized export/import procedures. Staying informed about updates to your primary applications and operating systems can help you anticipate and adapt to changes in clipboard behavior before they disrupt your workflow. Building redundancy into critical data transfer processes through multiple backup methods ensures continuity when primary clipboard operations fail. Additionally, investing time in learning alternative data transfer techniques specific to your most-used applications can provide valuable fallback options. As the computing landscape continues to evolve toward increased security, cross-platform compatibility, and cloud integration, users who understand the underlying principles of data transfer and maintain flexible, adaptable workflows will be best positioned to maintain productivity regardless of the technical challenges that emerge.