Your Lock Screen Is Leaking More Info Than You Think — Here's the Fix
Your smartphone's lock screen appears to be a protective barrier, but in reality, it's become a surprisingly transparent window into your personal world. While you may believe that requiring a PIN, password, or biometric authentication keeps your information secure, modern lock screens display far more sensitive data than most users realize. From notification previews revealing intimate conversations to widgets showing calendar appointments, location data, and even financial information, your lock screen has evolved into a comprehensive dashboard of your digital life that's visible to anyone who glances at your device. This exposure occurs whether your phone is sitting on a restaurant table, being handed to a friend to take a photo, or simply visible in your pocket or bag. The convenience features that make our devices more accessible have inadvertently created new privacy vulnerabilities that extend far beyond the traditional concept of device security. Understanding these risks and implementing proper safeguards isn't just about protecting against sophisticated hackers—it's about maintaining basic privacy in everyday situations where your phone might be visible to colleagues, family members, strangers, or even security cameras in public spaces.
1. The Notification Preview Problem
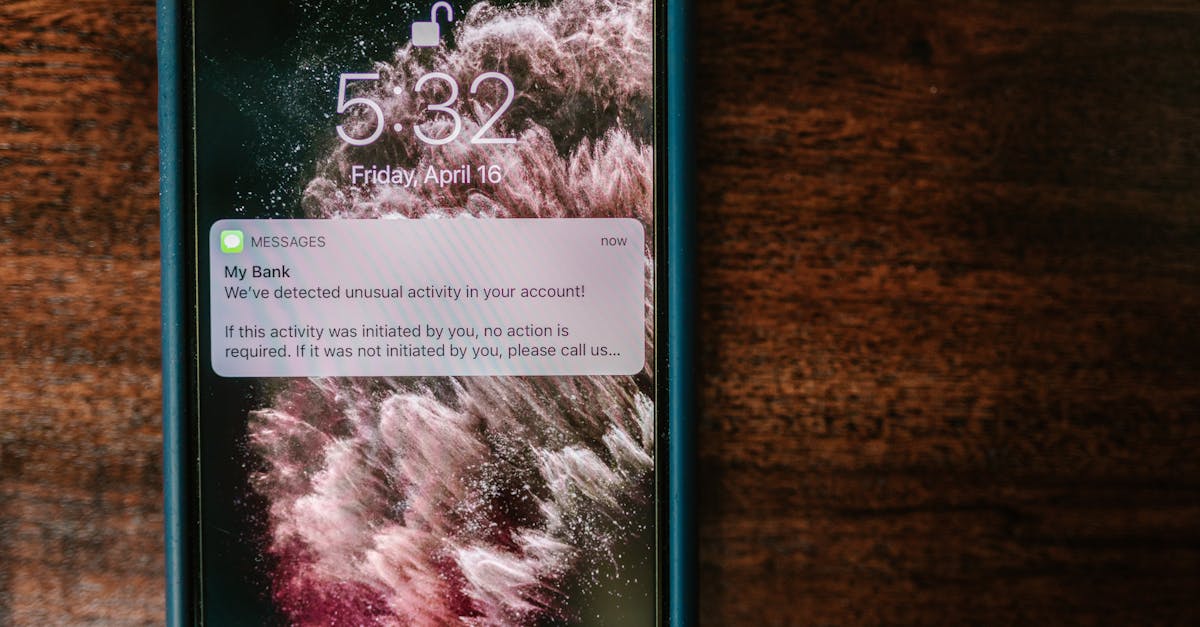
Notification previews on lock screens have become one of the most significant privacy leaks in modern smartphone usage, often revealing intimate details about your personal relationships, financial status, health conditions, and daily activities. When text messages, emails, dating app matches, medical appointment reminders, or banking alerts appear in full detail on your lock screen, they create a comprehensive profile of your life that's accessible to anyone within viewing distance. Research conducted by cybersecurity firms has demonstrated that skilled social engineers can gather enough information from lock screen notifications alone to craft convincing phishing attempts or social engineering attacks. The problem is compounded by the fact that many users receive dozens of notifications daily, creating a constant stream of personal information that's displayed without any authentication required. Popular messaging apps like WhatsApp, Telegram, and iMessage often show the sender's name and a preview of the message content, while email notifications might reveal sensitive work communications or personal correspondence. Dating apps frequently display profile photos and messages from potential matches, financial apps show transaction amounts and account balances, and health applications might reveal medical conditions or appointment details. This constant information leak occurs regardless of whether you're in a private setting or a public space, making your personal life an open book to anyone who happens to glance at your device.
2. Widget Vulnerabilities and Information Exposure

Lock screen widgets, while designed to provide quick access to important information, have become sophisticated data broadcasting systems that often reveal more personal details than their creators intended. Calendar widgets display upcoming appointments, meetings, and personal events with full titles and locations, potentially exposing sensitive business dealings, medical appointments, or personal relationships to anyone who can see your screen. Weather widgets might seem harmless, but they often reveal your current location or frequently visited places, creating a pattern that could be exploited by stalkers or criminals. Music widgets show your listening habits and preferences, which might seem trivial but can reveal cultural background, mood patterns, and even political leanings to those who understand how to interpret this data. News widgets can expose your political affiliations and interests, while fitness widgets might reveal your daily routines, exercise patterns, and health metrics. The aggregation of this information creates a detailed psychological and behavioral profile that extends far beyond what most users intend to share. Security researchers have demonstrated how this widget data can be systematically collected and analyzed to build comprehensive profiles of individuals, including their daily schedules, preferred locations, social connections, and personal interests. The convenience of having this information readily available comes at the cost of broadcasting intimate details about your life to anyone who can observe your device, whether that's a shoulder surfer on public transportation, a colleague during a meeting, or a stranger who finds your lost phone.
3. Biometric Authentication Isn't Bulletproof

While biometric authentication methods like fingerprint scanners, facial recognition, and iris scanning are generally more secure than traditional passwords, they introduce unique vulnerabilities that many users don't fully understand, particularly in the context of lock screen security. Facial recognition systems can be fooled by high-quality photographs, 3D-printed models, or even identical twins, and they often fail to work properly in low-light conditions, forcing users to rely on backup authentication methods that might be less secure. Fingerprint scanners, while more reliable, can be bypassed using lifted fingerprints from surfaces the user has touched, and they become completely useless if the user's fingers are wet, dirty, or injured. More concerning is the legal landscape surrounding biometric data, where courts in many jurisdictions have ruled that law enforcement can compel individuals to unlock their devices using biometric methods, while password disclosure remains protected under Fifth Amendment rights in the United States. The convenience of biometric authentication often leads users to disable additional security measures, creating a false sense of security that can be exploited by sophisticated attackers or even family members and friends who have observed the user's biometric patterns. Additionally, biometric data stored on devices, while typically encrypted and stored in secure enclaves, represents a permanent identifier that cannot be changed if compromised, unlike passwords or PINs that can be updated. The integration of biometric systems with lock screen features also means that partial authentication might grant access to sensitive information displayed on the lock screen itself, creating a graduated exposure risk that many users haven't considered.
4. Location Services and Geolocation Leaks

Location-based services integrated into lock screen functionality create persistent privacy risks that extend far beyond simple geographic coordinates, often revealing detailed patterns about your daily life, relationships, and personal habits. Lock screen widgets that display location-based information, such as nearby restaurants, traffic conditions, or weather for your current area, continuously broadcast your whereabouts to anyone who can see your device. This information becomes particularly sensitive when combined with time stamps, as it creates a detailed log of your movements that could be used to infer where you work, live, shop, and spend your leisure time. Many smartphones automatically display location-based suggestions on the lock screen, such as estimated travel times to frequently visited locations, which can reveal your home and work addresses, as well as places you visit regularly for personal reasons. The aggregation of this location data over time creates what security researchers call a "digital shadow" that can be more revealing than users realize, potentially exposing sensitive information about medical appointments, political activities, religious practices, or personal relationships. Stalkers, domestic abusers, and criminals have increasingly sophisticated methods for gathering and interpreting this location data, often combining information from multiple sources to build comprehensive profiles of their targets' movements and habits. Even seemingly innocent features like automatic check-ins, location-based reminders, or travel time notifications can provide enough information for malicious actors to predict your future whereabouts or identify vulnerable moments in your routine. The persistent nature of location tracking means that this information is continuously updated and displayed, creating an ongoing privacy risk that many users underestimate.
5. Third-Party App Integration Risks
The integration of third-party applications with lock screen functionality has created a complex ecosystem of privacy vulnerabilities that extend far beyond the control of device manufacturers, often involving data sharing practices that users don't fully understand or consent to. Social media applications frequently push notifications to lock screens that reveal personal relationships, political opinions, and social activities through post previews, comment notifications, and friend suggestions. Dating apps display profile photos and messages that can expose sexual orientation, relationship status, and personal preferences to anyone who can see the device. Financial applications show transaction notifications, account balances, and spending patterns that could be exploited by criminals or used for social engineering attacks. Health and fitness apps often display sensitive medical information, medication reminders, and health metrics that should remain private. The problem is compounded by the fact that many third-party applications have their own privacy policies and data handling practices that may be less stringent than those of the device manufacturer, creating additional vectors for data exposure and misuse. These applications often request extensive permissions that allow them to access and display information from other apps, creating a web of interconnected data sharing that can amplify privacy risks exponentially. Security researchers have documented cases where malicious applications have exploited lock screen integration to gather information about users' other installed apps, usage patterns, and personal data. The convenience of having all your important information accessible from the lock screen comes at the cost of trusting numerous third-party developers with sensitive personal data, and many users are unaware of the extent to which their information is being shared and potentially monetized by these app developers.
6. Voice Assistant Vulnerabilities

Voice assistants integrated into lock screen functionality represent a significant and often overlooked attack vector that can expose sensitive information through both intentional queries and accidental activations. Modern smartphones allow voice assistants like Siri, Google Assistant, and Alexa to respond to voice commands even when the device is locked, potentially allowing unauthorized users to access personal information, send messages, make calls, or control smart home devices without any authentication. These systems can be triggered by similar-sounding phrases, background conversations, or even audio from television shows and radio programs, leading to unintended activations that might record private conversations or execute unwanted commands. The voice recognition technology, while sophisticated, isn't perfect at distinguishing between authorized users and potential attackers, especially in noisy environments or when users have colds or other conditions that affect their voice patterns. Security researchers have demonstrated various attacks against voice assistant systems, including the use of ultrasonic frequencies that are inaudible to humans but can trigger device responses, and the exploitation of voice synthesis technology to mimic authorized users' voices. The integration of voice assistants with other smart devices and services means that a compromised voice assistant can potentially access a wide range of personal information and connected systems, from calendar appointments and contact lists to home security systems and financial accounts. Many users are unaware that voice assistant interactions are often recorded and stored by service providers, creating additional privacy concerns about how this data is used, shared, and protected. The convenience of hands-free interaction comes with the risk of unintended information disclosure and unauthorized access, particularly in environments where multiple people might be present or where background noise could trigger false activations.
7. Emergency Information and Medical ID Exposure

Emergency information features, while potentially life-saving, create significant privacy vulnerabilities by making sensitive personal and medical information accessible without any device authentication, often revealing far more about users than they realize or intend. Medical ID features on smartphones typically display critical health information, emergency contacts, medical conditions, medications, allergies, and blood type directly from the lock screen, ostensibly to help first responders in emergency situations. However, this information is accessible to anyone who knows how to access the emergency features, which are often prominently displayed and easy to find. The medical information stored in these systems can reveal sensitive details about mental health conditions, chronic diseases, prescription medications, and personal relationships that could be used for discrimination, social engineering, or identity theft. Emergency contact information often includes family members, romantic partners, and close friends, potentially exposing personal relationships and social networks to unauthorized viewers. Some users include additional personal information in their medical IDs, such as insurance information, doctor contact details, or even personal preferences about medical treatment, further expanding the potential for privacy violations. The challenge with emergency information features is balancing the legitimate need for first responders to access critical medical information with the privacy risks of making this data broadly accessible. Security researchers have noted that criminals and social engineers increasingly target emergency information as a source of personal data that can be used for various malicious purposes, from crafting convincing phishing attempts to gathering information for identity theft or fraud. The permanent visibility of this information means that anyone who gains physical access to the device, even briefly, can gather detailed personal and medical information about the user.
8. Corporate and BYOD Security Implications

The bring-your-own-device (BYOD) trend in corporate environments has created complex security challenges related to lock screen information exposure, where personal privacy concerns intersect with corporate data protection requirements in ways that many organizations and employees don't fully understand. Corporate email notifications, calendar appointments, and business communications displayed on personal device lock screens can expose sensitive company information to unauthorized viewers, potentially violating confidentiality agreements, regulatory requirements, or competitive intelligence protections. Employees often receive notifications about confidential projects, financial information, personnel matters, and strategic business decisions directly on their lock screens, creating risks for corporate espionage and data breaches. The problem is compounded by the fact that personal and professional information is often intermingled on the same device, making it difficult to implement security controls that protect corporate data without affecting personal privacy. Many organizations struggle to balance employee privacy rights with the need to protect sensitive business information, leading to inconsistent or inadequate security policies that leave both personal and corporate data vulnerable. Mobile device management (MDM) solutions can provide some protection, but they often require extensive permissions that many employees are reluctant to grant on their personal devices, and they may not address all the ways that information can leak through lock screen features. The global nature of modern business means that devices may be subject to different legal and regulatory requirements in different jurisdictions, complicating efforts to implement consistent security controls. Security incidents involving lock screen information exposure can have serious consequences for both individuals and organizations, including regulatory fines, competitive disadvantages, and reputational damage that extends far beyond the initial privacy violation.
9. Children and Family Privacy Considerations
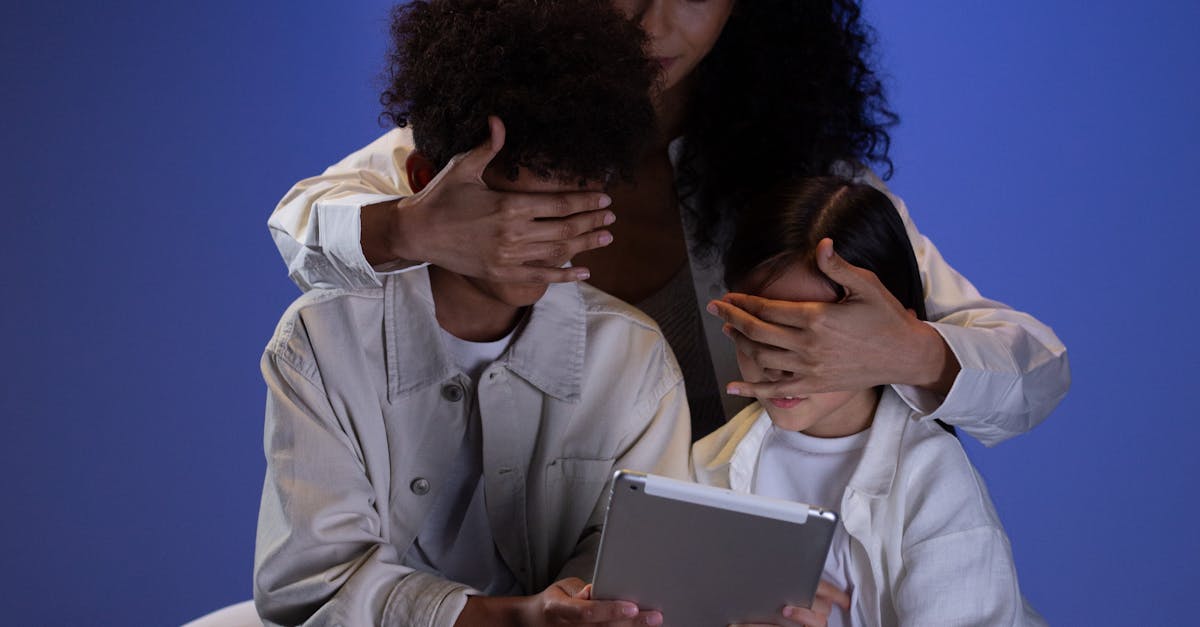
Family dynamics and child safety considerations add additional layers of complexity to lock screen privacy, where well-intentioned parental oversight can conflict with legitimate privacy needs, and where children's developing understanding of digital privacy creates unique vulnerabilities. Parents often configure family sharing features and parental controls that display information about children's activities, locations, and communications on lock screens, potentially exposing sensitive information about minors to anyone who can see the parent's device. Children and teenagers, meanwhile, may not fully understand the privacy implications of their lock screen configurations, often prioritizing convenience and social connectivity over security considerations. The integration of educational apps, social media platforms, and gaming services with lock screen notifications means that information about children's academic performance, social relationships, and online activities may be visible to family members, friends, or strangers who can see their devices. Family calendar sharing and location tracking features, while useful for coordination and safety, can reveal detailed information about children's schedules, activities, and whereabouts that could be exploited by predators or other malicious actors. The challenge for families is establishing appropriate boundaries between legitimate safety concerns and privacy rights, particularly as children mature and develop their own sense of digital autonomy. Many parents are unaware of the extent to which their own devices may be displaying information about their children's activities, and children often lack the technical knowledge or authority to properly configure their own privacy settings. The long-term implications of childhood digital privacy violations are still being understood, but research suggests that early exposure to privacy violations can affect children's development of healthy digital boundaries and their understanding of personal privacy rights.
10. Comprehensive Solutions and Best Practices

Implementing effective lock screen privacy protection requires a multi-layered approach that balances security, convenience, and usability while addressing the diverse ways that personal information can be exposed through modern smartphone interfaces. The most fundamental step is disabling notification previews for sensitive applications, configuring notifications to show only that a message or alert has been received without displaying the content, sender information, or other identifying details. Users should carefully review and customize which applications are permitted to display information on the lock screen, prioritizing only those that provide essential functionality without exposing sensitive personal data. Biometric authentication should be supplemented with strong backup passwords or PINs, and users should understand the legal and practical limitations of biometric security in their jurisdiction. Location services should be configured to minimize unnecessary data sharing, with particular attention to widgets and features that continuously broadcast location information. Voice assistant access from lock screens should be disabled or carefully configured to prevent unauthorized access, and users should regularly review voice assistant settings and recorded interactions. Emergency information features should be configured to include only essential medical information, avoiding unnecessary personal details that could be exploited for non-emergency purposes. Regular security audits of lock screen configurations, application permissions, and privacy settings should be conducted to ensure that new features or app updates haven't introduced additional privacy risks. Organizations implementing BYOD policies should provide clear guidelines and technical support for employees to properly configure their personal devices, while families should establish age-appropriate privacy education and device management practices. Ultimately, protecting lock screen privacy requires ongoing vigilance and education, as the rapidly evolving landscape of mobile technology continues to introduce new features and potential vulnerabilities that users must understand and address proactively.