The Hidden Clipboard That's Been Storing Everything You Copy
# The Hidden Clipboard That's Been Storing Everything You Copy: A Deep Dive Into Digital Memory's Secret Vault
In the vast ecosystem of modern computing, there exists a silent guardian of your digital activities—a hidden repository that meticulously catalogs every piece of text, image, and data you've ever copied. This invisible archive, known as the clipboard history or clipboard cache, operates behind the scenes of your daily computing experience, creating an extensive digital footprint that most users remain completely unaware of. While you may think that copying and pasting is a temporary action that leaves no trace, the reality is far more complex and potentially concerning. Modern operating systems, from Windows 10's revolutionary clipboard history feature to macOS's sophisticated Universal Clipboard, have transformed the simple act of copying into a comprehensive data collection mechanism. This hidden functionality extends beyond basic text snippets to include sensitive information such as passwords, financial data, personal communications, and confidential documents. Understanding this invisible digital memory is crucial in our privacy-conscious era, as it reveals how our most casual computing habits contribute to an ever-growing archive of personal information that could potentially be accessed, analyzed, or compromised. The implications stretch far beyond convenience, touching on fundamental questions of digital privacy, data security, and user autonomy in an increasingly connected world.
## Section 2: The Evolution of Clipboard Technology - From Simple Copy-Paste to Comprehensive Data Logging
The clipboard's journey from a basic temporary storage mechanism to a sophisticated data retention system represents one of the most significant yet overlooked developments in personal computing history. Originally conceived in the 1970s at Xerox PARC as part of the groundbreaking Alto computer system, the clipboard was designed as a simple buffer that would temporarily hold copied data until it was pasted elsewhere. This rudimentary system could only store one item at a time, and the data would be immediately overwritten with each new copy operation. However, as computing power increased and storage became more affordable, software developers began to recognize the potential for enhanced clipboard functionality. The introduction of multi-item clipboard managers in the 1990s marked the first significant evolution, allowing users to maintain a history of copied items. What began as third-party utilities gradually became integrated into operating systems themselves, with Apple introducing clipboard synchronization across devices through iCloud and Microsoft implementing comprehensive clipboard history in Windows 10. Today's clipboard systems are sophisticated databases capable of storing thousands of entries, complete with timestamps, source applications, and metadata. This evolution reflects a broader trend in computing toward persistent data retention, where temporary actions increasingly leave permanent digital traces, fundamentally altering the relationship between user intent and data persistence.
1. Windows Clipboard History - Microsoft's Comprehensive Data Collection System

Microsoft's implementation of clipboard history in Windows 10 represents perhaps the most ambitious and comprehensive approach to clipboard data retention in mainstream computing. Activated through the Windows + V keyboard shortcut, this system maintains a detailed log of copied items that can span weeks or even months, depending on system configuration and available storage. The Windows clipboard history doesn't merely store text snippets; it captures rich formatting, images, files, and even complex data structures from various applications. Each entry is meticulously cataloged with timestamps, source applications, and usage frequency, creating a detailed profile of user behavior and information consumption patterns. The system's integration with Microsoft's cloud services means that clipboard data can be synchronized across multiple devices, creating a comprehensive cross-platform archive of copied information. This functionality extends to Microsoft's enterprise solutions, where clipboard history can be subject to corporate data retention policies and compliance requirements. The technical implementation involves sophisticated memory management algorithms that balance performance with storage efficiency, using compression techniques and intelligent caching to maintain responsiveness while preserving extensive historical data. Privacy controls allow users to clear history or exclude specific applications, but the default behavior is comprehensive retention, meaning most users unknowingly accumulate vast archives of copied data. The system's deep integration with Windows' security framework also means that clipboard data is subject to the same encryption and access controls as other system data, though this protection is only as strong as the user's overall system security posture.
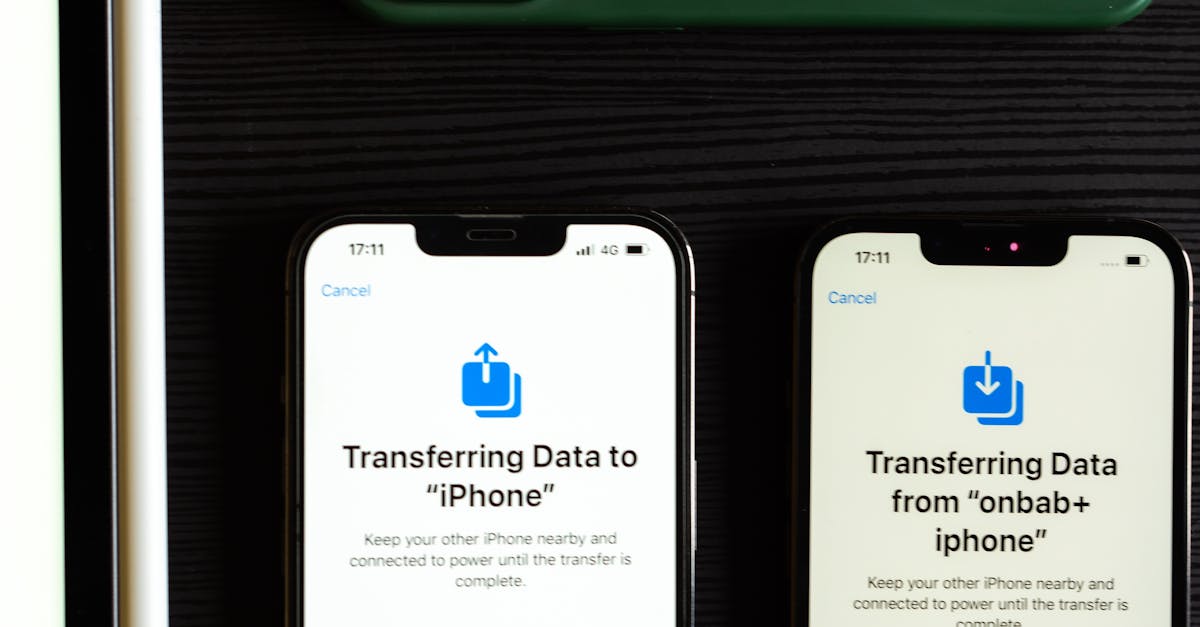
2. macOS Universal Clipboard and Handoff - Apple's Cross-Device Data Synchronization

Apple's approach to clipboard functionality through the Universal Clipboard and Handoff features represents a sophisticated ecosystem-wide data synchronization system that extends far beyond traditional copy-paste operations. Introduced with macOS Sierra and iOS 10, Universal Clipboard creates a seamless experience where copied content on one Apple device automatically becomes available on all other devices signed into the same Apple ID. This system operates through a complex network of encrypted peer-to-peer connections and iCloud synchronization, ensuring that clipboard data is not only preserved locally but also distributed across an entire device ecosystem. The technical implementation involves sophisticated conflict resolution algorithms that manage simultaneous clipboard operations across multiple devices, timestamp-based priority systems that determine which copied item takes precedence, and intelligent caching mechanisms that balance immediate availability with network efficiency. Beyond simple text and images, Universal Clipboard can synchronize rich media content, formatted documents, and even application-specific data structures, creating a comprehensive cross-platform clipboard experience. The system's integration with Apple's broader Continuity framework means that clipboard data becomes part of a larger ecosystem of synchronized user activities, including browsing history, application states, and document access patterns. Privacy implications are significant, as clipboard data is encrypted in transit and at rest, but the comprehensive nature of the synchronization means that sensitive information copied on one device immediately becomes accessible across all connected devices. The persistence of this data varies based on device storage and iCloud settings, but items can remain accessible for extended periods, creating a detailed archive of user information consumption and sharing patterns across the entire Apple ecosystem.
3. Third-Party Clipboard Managers - The Underground Economy of Data Retention

The thriving ecosystem of third-party clipboard managers reveals the extent to which users and organizations seek enhanced clipboard functionality, often unknowingly creating even more comprehensive data retention systems than those built into operating systems. Applications like ClipX, Ditto, CopyQ, and Alfred's clipboard history feature offer sophisticated functionality that can store thousands of clipboard entries with advanced search capabilities, categorization systems, and even cloud synchronization across platforms. These tools often provide features that surpass native operating system implementations, including the ability to store clipboard history indefinitely, create custom categories and tags for copied items, and implement advanced search algorithms that can locate specific content from vast archives of copied data. The technical sophistication of these applications is remarkable, with some implementing full-text search across years of clipboard history, optical character recognition for copied images, and even machine learning algorithms that predict which clipboard items users are most likely to need. However, this enhanced functionality comes with significant privacy implications, as third-party clipboard managers often have extensive system access permissions and may store data in formats and locations that are not subject to the same security protections as native system functions. Many of these applications also offer cloud synchronization features, meaning clipboard data may be transmitted to and stored on third-party servers, potentially subject to different privacy policies and security standards. The business models of some clipboard managers involve data analytics and user behavior tracking, raising questions about how copied information might be analyzed or monetized. Enterprise versions of these tools often include features for administrators to monitor and analyze employee clipboard usage, creating detailed profiles of information access and sharing patterns within organizations.
4. The Invisible Data Trail - What Information Is Actually Being Stored

The scope and nature of information captured by modern clipboard systems extends far beyond what most users realize, creating comprehensive digital profiles that reveal intimate details about personal and professional activities. Every copied password, financial account number, personal message, confidential document excerpt, and private communication becomes part of a persistent digital record that can span months or years. The technical implementation of clipboard storage systems means that even seemingly innocuous copied text can contain hidden metadata that reveals source applications, timestamps, user contexts, and system states at the time of copying. Images copied to the clipboard often retain extensive EXIF data, including location information, camera settings, and editing history, while formatted documents can include hidden revision tracking, author information, and embedded objects that create additional data trails. The persistence mechanisms employed by different systems vary significantly, with some maintaining clipboard data in easily accessible plain text files, while others use encrypted databases or compressed archives that require specialized tools to access. Cross-application data sharing through clipboard operations can also create unexpected information leakage, where copying content from secure applications results in data being accessible to other applications with clipboard access permissions. The temporal aspect of clipboard storage is particularly significant, as items copied during sensitive activities—such as online banking, medical consultations, or confidential business communications—remain accessible long after the original context has been forgotten. Modern clipboard systems also capture rich formatting and structural information, meaning that copied content often includes more data than is visible to the user, such as hidden hyperlinks, embedded scripts, or formatting codes that can reveal additional information about the source and context of the copied material.
5. Privacy Implications and Security Vulnerabilities

The comprehensive data retention capabilities of modern clipboard systems create significant privacy vulnerabilities that most users are completely unaware of, transforming routine computing activities into potential security risks. The persistent nature of clipboard storage means that sensitive information such as passwords, social security numbers, credit card details, and private communications can remain accessible on a system long after the user believes they have been securely handled. This creates multiple attack vectors for malicious actors, including physical access to devices where clipboard history can be easily retrieved, malware that specifically targets clipboard data for credential harvesting, and social engineering attacks that exploit users' lack of awareness about clipboard persistence. The cross-device synchronization features implemented by major operating systems compound these risks by ensuring that sensitive clipboard data is transmitted across networks and stored on multiple devices, potentially expanding the attack surface for data breaches. Enterprise environments face particular challenges, as employee clipboard activities can inadvertently expose confidential business information, intellectual property, or customer data through persistent storage systems that may not be subject to the same security controls as other corporate data repositories. The technical implementation of clipboard encryption varies significantly across platforms and applications, with some systems storing clipboard data in plain text files that can be easily accessed by anyone with system privileges, while others implement sophisticated encryption schemes that provide robust protection. However, even encrypted clipboard systems can be vulnerable to attacks that target the decryption keys or exploit weaknesses in the encryption implementation. The integration of clipboard systems with cloud services introduces additional privacy concerns, as copied data may be transmitted to and stored on remote servers operated by third parties, potentially subject to government surveillance, corporate data mining, or security breaches that could expose vast amounts of personal information.
6. Corporate and Enterprise Clipboard Monitoring

In corporate environments, clipboard monitoring and data retention systems have evolved into sophisticated tools for information security, compliance monitoring, and employee surveillance, creating complex ethical and legal frameworks around workplace privacy. Enterprise-grade clipboard management solutions offer administrators unprecedented visibility into employee information handling practices, with the ability to log, analyze, and report on all clipboard activities across organizational networks. These systems can automatically detect and flag sensitive information such as social security numbers, credit card data, or proprietary business information when it appears in clipboard operations, triggering security alerts or compliance workflows. The technical implementation of enterprise clipboard monitoring often involves deep integration with existing security infrastructure, including data loss prevention (DLP) systems, security information and event management (SIEM) platforms, and identity management solutions. Advanced enterprise clipboard systems can implement policy-based controls that automatically prevent certain types of information from being copied, encrypt clipboard data based on classification levels, or require additional authentication for accessing clipboard history containing sensitive information. The legal and regulatory implications of corporate clipboard monitoring are complex, with different jurisdictions having varying requirements for employee notification, consent, and data retention. Some organizations use clipboard monitoring as part of broader insider threat detection programs, analyzing patterns in clipboard usage to identify potential security risks or policy violations. The integration of artificial intelligence and machine learning into enterprise clipboard systems enables sophisticated behavioral analysis that can detect anomalous copying patterns, identify potential data exfiltration attempts, or predict security risks based on clipboard usage trends. However, the comprehensive nature of clipboard monitoring raises significant concerns about employee privacy, workplace surveillance, and the potential for misuse of detailed information about employee activities and information consumption patterns.
7. Mobile Devices and Cross-Platform Synchronization
The ubiquity of mobile devices has fundamentally transformed clipboard functionality from a single-device feature into a comprehensive cross-platform data synchronization system that creates persistent digital trails across multiple devices and platforms. Modern smartphones and tablets implement sophisticated clipboard systems that not only store extensive histories of copied content but also synchronize this data across devices through cloud services, creating comprehensive archives of user information consumption patterns. The technical challenges of mobile clipboard implementation are significant, involving careful balance between functionality and battery life, sophisticated memory management to handle limited storage resources, and complex synchronization protocols that ensure data consistency across devices with varying connectivity patterns. Mobile operating systems like iOS and Android have implemented increasingly sophisticated clipboard features, including the ability to detect and categorize different types of copied content, provide intelligent suggestions based on clipboard history, and integrate clipboard data with other system features such as predictive text and application shortcuts. The cross-platform nature of modern clipboard systems means that content copied on a mobile device can immediately become available on desktop computers, tablets, and other connected devices, creating seamless user experiences but also expanding the potential attack surface for security breaches. Privacy implications are particularly significant in mobile environments, where clipboard data may be accessible to a wide range of applications, transmitted over various network connections, and stored in cloud services that may be subject to different privacy policies and security standards. The integration of mobile clipboard systems with virtual assistants and AI-powered features creates additional privacy concerns, as copied content may be analyzed for pattern recognition, used to improve predictive algorithms, or incorporated into broader user profiling systems. Mobile device management (MDM) solutions in enterprise environments often include sophisticated clipboard monitoring and control features, allowing organizations to implement policies that restrict clipboard functionality, monitor clipboard usage, or prevent sensitive information from being copied on mobile devices.
8. Digital Forensics and Legal Implications

The persistent nature of modern clipboard systems has created new opportunities and challenges in digital forensics, transforming routine clipboard data into valuable evidence that can provide crucial insights into user activities, information access patterns, and digital behavior timelines. Law enforcement agencies and digital forensics specialists have developed sophisticated techniques for extracting and analyzing clipboard data from various operating systems and applications, often revealing information that users believed had been temporarily handled and forgotten. The technical aspects of clipboard forensics involve understanding the storage mechanisms used by different systems, developing tools to extract data from encrypted or compressed clipboard archives, and implementing analysis techniques that can reconstruct user activities based on clipboard usage patterns. Legal frameworks around clipboard data as evidence are still evolving, with courts grappling with questions about the reasonable expectation of privacy for clipboard contents, the admissibility of clipboard data as evidence, and the proper procedures for collecting and preserving clipboard evidence. The comprehensive nature of modern clipboard systems means that forensic analysis can reveal detailed timelines of user activities, including when specific information was accessed, copied, and potentially shared with other applications or users. Cross-device synchronization features create additional complexity for digital forensics, as clipboard evidence may be distributed across multiple devices and cloud services, requiring coordinated collection efforts and sophisticated analysis techniques to reconstruct complete user activity profiles. The integration of clipboard systems with other digital evidence sources, such as browser history, application logs, and network traffic analysis, enables forensic investigators to develop comprehensive pictures of user behavior and information handling practices. However, the use of clipboard data as evidence also raises significant privacy concerns and legal questions about the scope of digital surveillance, the rights of individuals to control their digital information, and the appropriate limits on law enforcement access to persistent digital records of routine computing activities.
9. Taking Control - Managing and Securing Your Clipboard Data

Understanding and managing clipboard data retention has become an essential aspect of digital privacy and security, requiring users to actively engage with settings and practices that most never consider but that can significantly impact their personal information security. The first step in clipboard management involves understanding the specific retention policies and storage mechanisms used by your operating system and applications, which can often be configured through privacy settings, system preferences, or application-specific controls. Windows users can disable clipboard history through the Settings app, clear existing clipboard data, and configure which applications have access to clipboard functionality, while macOS users can manage Universal Clipboard settings through System Preferences and implement third-party solutions for more granular control. Mobile device users should review clipboard permissions for installed applications, understand how clipboard data is synchronized across devices, and consider implementing additional security measures such as clipboard clearing applications or privacy-focused keyboards that minimize data retention. Enterprise users should work with IT departments to understand corporate clipboard monitoring policies, implement appropriate security practices for handling sensitive information, and consider using specialized secure communication tools for confidential information that bypasses clipboard systems entirely. Technical solutions for enhanced clipboard security include using clipboard managers with strong encryption, implementing automatic clipboard clearing policies, and utilizing virtual machines or sandboxed environments for handling sensitive information. Regular security audits should include reviewing clipboard history, understanding what information has been stored, and implementing appropriate data retention policies that balance convenience with privacy protection. Advanced users might consider implementing custom scripts or applications that automatically clear clipboard data after specified time periods, encrypt clipboard contents, or provide detailed logging of clipboard activities for security monitoring purposes. The key to effective clipboard management lies in understanding that this seemingly simple computing feature has evolved into a comprehensive data retention system that requires active management and security consideration as part of a broader digital privacy strategy.