How to Hide Apps Without Deleting Them or Using a Folder
# How to Hide Apps Without Deleting Them or Using a Folder: 11 Clever Methods to Keep Your Digital Life Private
In today's hyper-connected world, our smartphones have become intimate repositories of our personal lives, containing everything from banking applications to dating profiles, work documents to private messaging platforms. While the conventional wisdom suggests organizing apps into folders or simply deleting unwanted applications, there exists a sophisticated middle ground that allows users to maintain complete access to their digital tools while keeping them discretely hidden from prying eyes. The art of concealing applications without deletion or folder organization represents a nuanced approach to digital privacy that acknowledges the reality of our modern lives—we need access to sensitive apps, but we don't necessarily want them displayed prominently on our home screens. Whether you're protecting financial information from curious family members, maintaining professional boundaries, or simply decluttering your interface while preserving functionality, mastering these techniques transforms your device into a more secure and personally tailored digital environment. This comprehensive exploration will unveil eleven distinct methodologies that leverage built-in system features, creative workarounds, and strategic interface manipulation to achieve seamless app concealment across various operating systems and device types.
1. Utilizing Built-in App Library Features on iOS
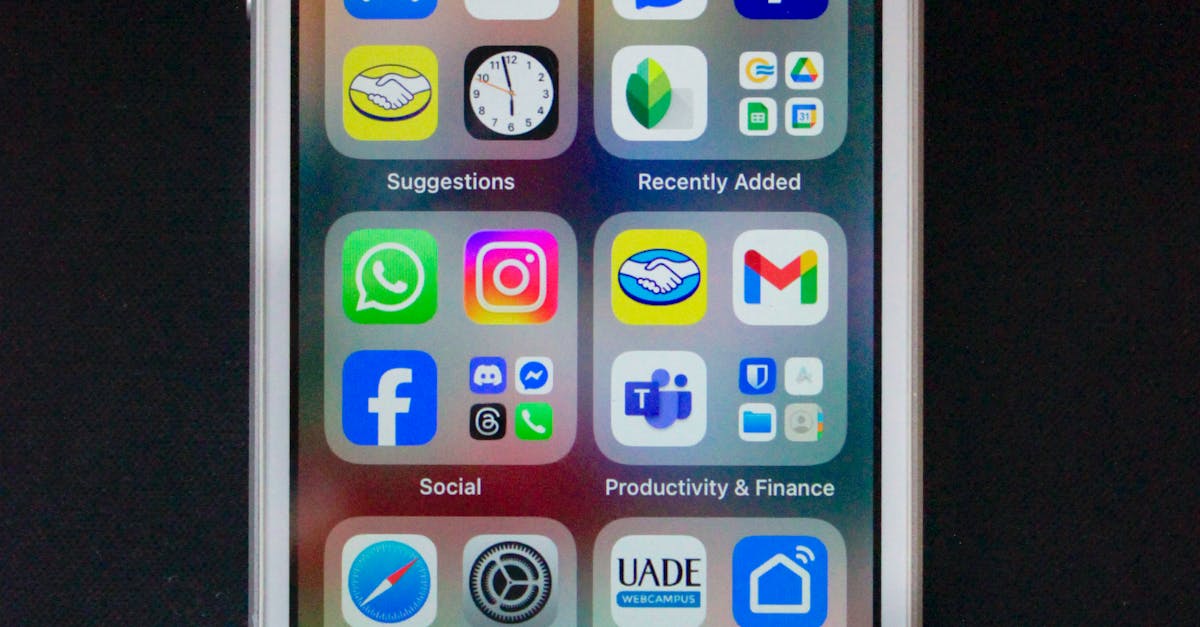
Apple's iOS ecosystem provides users with a remarkably elegant solution through its App Library feature, introduced in iOS 14, which automatically categorizes and organizes applications while allowing for sophisticated hiding mechanisms. By removing apps from the home screen while keeping them accessible through the App Library, users can maintain a clean, minimalist interface without sacrificing functionality. This process involves long-pressing the desired application icon, selecting "Remove App," and then choosing "Remove from Home Screen" rather than "Delete App." The application remains fully functional and accessible through the App Library, which can be reached by swiping left past the final home screen page. This method proves particularly effective for applications that are used infrequently but must remain available, such as banking apps, utility applications, or specialized work tools. The App Library's intelligent categorization system automatically sorts these hidden applications into relevant categories like "Finance," "Productivity," or "Utilities," making them discoverable when needed while keeping them out of immediate view. Additionally, users can leverage Spotlight Search to quickly access these hidden applications by simply swiping down on any home screen and typing the app name, creating a seamless user experience that balances privacy with accessibility.
2. Leveraging Android's App Drawer and Hidden Features

Android's inherently flexible architecture offers multiple pathways for concealing applications through its app drawer system and manufacturer-specific customizations that provide granular control over app visibility. Most Android devices feature a dedicated app drawer accessible through an upward swipe or app drawer icon, where users can hide specific applications from the home screen while maintaining full access through the drawer interface. Samsung devices, for instance, offer a "Hide Apps" feature within the app drawer settings, allowing users to select multiple applications for concealment behind a simple toggle switch. Google Pixel devices and stock Android implementations provide similar functionality through the app drawer's settings menu, where users can disable specific apps from appearing in the main interface. The process typically involves accessing the app drawer, navigating to the settings or menu options (often represented by three dots), and selecting "Hide Apps" or "App Visibility" options. Once hidden, these applications can only be accessed through specific methods such as typing their names in the app drawer search function or using alternative launchers that provide additional hiding capabilities. This approach proves particularly valuable for users who want to maintain a professional appearance on their device while keeping personal applications readily accessible through alternative navigation methods.
3. Mastering Screen Time and Restrictions Settings
Both iOS and Android platforms offer sophisticated screen time and parental control features that can be repurposed for personal app hiding, creating an additional layer of privacy through restriction-based concealment methods. On iOS devices, the Screen Time feature allows users to set app limits and restrictions that effectively hide applications during specified periods or until specific conditions are met. By navigating to Settings > Screen Time > App Limits, users can create custom restrictions for individual applications or entire app categories, causing them to become inaccessible and effectively hidden during designated time periods. This method proves particularly useful for creating work-life boundaries, where social media or entertainment apps become hidden during professional hours. Android's Digital Wellbeing and parental controls offer similar functionality through app timers and focus modes that can temporarily hide distracting applications. The Focus Mode feature, available on many Android devices, allows users to select specific apps to hide during designated periods, creating a customized interface that adapts to different life contexts. Advanced users can leverage these features creatively by setting extremely long time limits or using complex scheduling to effectively hide applications while maintaining the ability to access them through override options when necessary, creating a sophisticated hiding system that appears to be productivity-focused rather than privacy-driven.
4. Creating Invisible Icons and Transparent Shortcuts

The technique of creating invisible or transparent app icons represents one of the most creative approaches to app concealment, utilizing visual camouflage to hide applications in plain sight on your device's home screen. This method involves creating custom app shortcuts or widgets with transparent or nearly invisible icons that blend seamlessly with your wallpaper, making applications functionally invisible while keeping them easily accessible to those who know their precise locations. On iOS devices, this can be accomplished through the Shortcuts app, where users can create custom shortcuts that launch specific applications while using transparent or minimal icon designs. The process involves creating a new shortcut, adding the "Open App" action, selecting the target application, and then customizing the shortcut's icon with a transparent image or one that matches the wallpaper perfectly. Android users can achieve similar results through various launcher applications like Nova Launcher or Action Launcher, which allow for extensive icon customization and transparency options. Third-party apps like "Invisible Icon" or "Transparent Icon" specifically cater to this need, providing pre-made transparent icons that can be applied to any application shortcut. This method proves particularly effective when combined with strategic placement on the home screen, positioning invisible icons in locations that appear empty but are actually functional app launchers, creating a sophisticated hiding system that maintains quick access while providing complete visual concealment.
5. Exploiting Search-Only Access Methods
Transforming your device into a search-centric interface effectively hides applications by removing them from visual browsing while maintaining instant access through intelligent search functions, creating a minimalist approach that prioritizes functionality over visual organization. This methodology involves removing applications from all visible home screen locations and relying exclusively on search mechanisms to launch them, effectively creating a "hidden by default" system where only actively searched applications become accessible. iOS users can implement this approach by removing apps from the home screen and App Library's main view, then accessing them exclusively through Spotlight Search by swiping down on any screen and typing the application name. This creates a clean, distraction-free interface while maintaining full functionality for users who prefer keyboard-driven navigation. Android devices offer even more sophisticated search-only access through Google's search integration and custom launchers that prioritize search functionality over traditional icon-based navigation. Launchers like "Niagara Launcher" or "Search Based Launcher" are specifically designed around this concept, providing minimal interfaces where applications are accessed primarily through search queries rather than visual browsing. This approach proves particularly valuable for power users who prefer efficiency over visual organization, as it eliminates the cognitive overhead of scanning through multiple screens while providing instant access to any application through a simple search query, effectively hiding all applications while maintaining optimal accessibility.
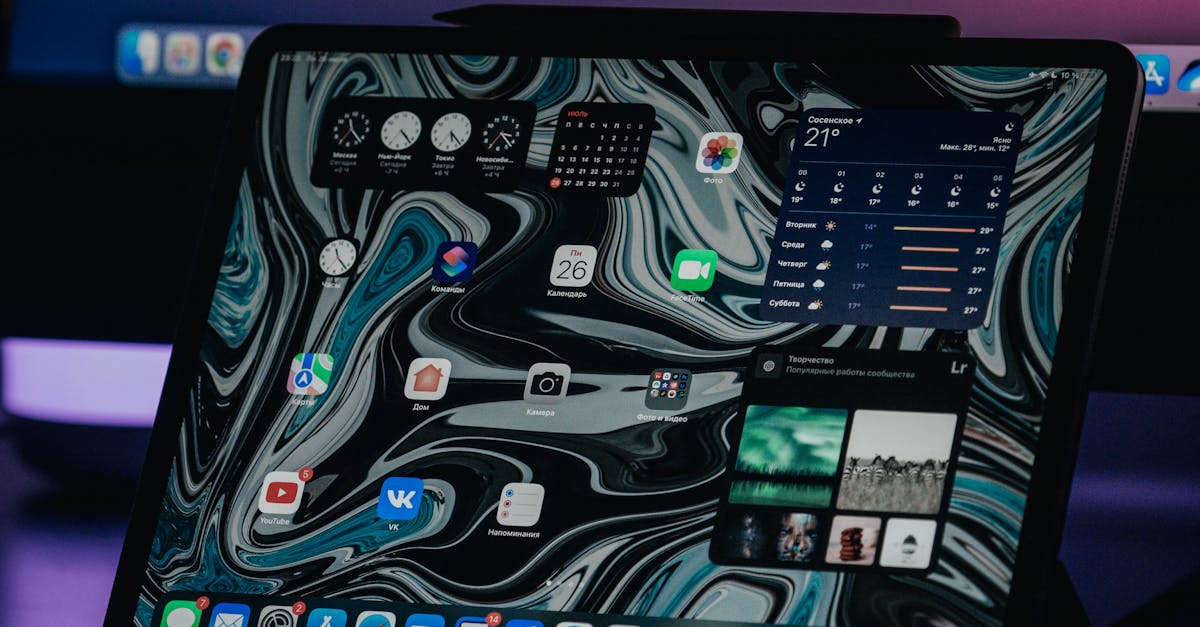
6. Utilizing Alternative Launchers and Custom Interfaces

Third-party launcher applications represent perhaps the most powerful and flexible approach to app concealment, offering extensive customization options that far exceed the capabilities of stock operating system interfaces. These specialized applications completely replace the default home screen experience, providing advanced hiding features, gesture controls, and sophisticated organization systems that can make applications virtually invisible to casual observers. Popular Android launchers like Nova Launcher, Action Launcher, and Apex Launcher offer built-in app hiding features that allow users to completely remove applications from the app drawer and home screen while maintaining access through hidden gestures, secret menus, or password-protected sections. The setup process typically involves installing the preferred launcher, setting it as the default home screen application, and then configuring the hiding features through the launcher's settings menu. Many of these launchers support gesture-based access, where hidden applications can be launched through specific swipe patterns, double-taps, or multi-finger gestures that are invisible to casual users but provide instant access for the device owner. Some advanced launchers even support multiple user profiles or hidden workspaces that can be accessed through specific authentication methods, creating completely separate interface environments for different contexts. While iOS has more limited support for alternative launchers due to Apple's ecosystem restrictions, jailbroken devices can access similar functionality through specialized tweaks and custom interfaces that provide comparable hiding capabilities.
7. Implementing Gesture-Based Hidden Access

Gesture-based app launching represents an elegant solution that transforms simple finger movements into powerful hiding mechanisms, allowing users to access concealed applications through intuitive motions that appear meaningless to observers. This sophisticated approach leverages the natural touch interface of modern smartphones to create hidden access methods that feel organic and seamless while providing robust concealment for sensitive applications. Many custom launchers and specialized applications support gesture recognition, where specific swipe patterns, tap sequences, or multi-finger gestures can be programmed to launch hidden applications directly from any screen location. For example, a simple two-finger swipe upward might launch a banking application, while a circular gesture could open a private messaging platform, creating a personalized access system that bypasses traditional icon-based navigation entirely. iOS users can implement gesture-based access through the Shortcuts app combined with Accessibility features, creating custom gestures that trigger specific app launches through the AssistiveTouch functionality or Back Tap features. Android devices offer even more extensive gesture support through applications like "GMD GestureControl" or "All in one Gestures," which allow users to define complex gesture patterns for launching hidden applications from anywhere within the operating system. The key to effective gesture-based hiding lies in choosing movements that feel natural and memorable while remaining obscure enough to avoid accidental activation, creating a balance between accessibility and concealment that enhances both privacy and user experience.
8. Leveraging Widget-Based Concealment Techniques
Widget-based concealment represents an innovative approach that disguises application access within seemingly innocent home screen elements, transforming functional widgets into covert launching mechanisms for hidden applications. This method exploits the visual familiarity of widgets to create hiding spots that blend seamlessly with typical home screen layouts while providing direct access to concealed applications through subtle interactions. Modern smartphones support interactive widgets that can perform complex actions beyond simple information display, making them ideal vehicles for hidden app launching. iOS users can create custom widgets through the Shortcuts app that appear as standard information widgets but actually function as application launchers when tapped or interacted with in specific ways. These widgets can be designed to mimic common elements like weather displays, calendar entries, or note previews while secretly providing access to hidden applications through tap, long-press, or swipe interactions. Android's widget system offers even more sophisticated concealment options through third-party widget applications that support hidden functionality and custom interactions. Applications like "KWGT" or "Zooper Widget" allow users to create completely custom widgets with hidden touch zones, secret gestures, or disguised buttons that launch specific applications while appearing to serve entirely different purposes. The effectiveness of widget-based concealment lies in choosing designs that match the user's typical home screen aesthetic while incorporating subtle interaction methods that provide reliable access without drawing attention from casual observers.
9. Employing Voice Command and Digital Assistant Integration

Voice-activated app launching provides an sophisticated concealment method that completely bypasses visual interfaces while maintaining instant access through natural language commands, creating a hands-free hiding system that appears to be simple convenience rather than deliberate concealment. This approach leverages the advanced voice recognition capabilities of modern digital assistants to create custom voice shortcuts that can launch hidden applications through personalized phrases or commands that are meaningful to the user but obscure to others. iOS users can create custom Siri shortcuts that respond to specific phrases, allowing applications to be launched through voice commands like "Hey Siri, check my investments" to open a banking app, or "Hey Siri, review my notes" to launch a private journaling application. The Shortcuts app provides extensive customization options for these voice commands, allowing users to create complex workflows that can launch applications, navigate to specific sections, or even perform multiple actions in sequence through a single voice command. Android devices offer similar functionality through Google Assistant integration and third-party voice command applications that support custom phrase recognition and app launching capabilities. Advanced users can create voice commands that sound like innocent requests but actually trigger specific application launches, such as "OK Google, what's the weather like?" configured to launch a private messaging app instead of providing weather information. This method proves particularly valuable in situations where discrete access is required, as voice commands can be issued quietly or in contexts where speaking to a device appears natural, providing complete concealment while maintaining effortless accessibility.
10. Advanced Security Integration and Biometric Concealment

The integration of biometric security features with app concealment creates the most sophisticated hiding system available, combining multiple authentication factors with advanced concealment techniques to provide enterprise-level privacy for personal applications. This approach leverages fingerprint recognition, facial authentication, voice recognition, and behavioral biometrics to create multi-layered access systems that not only hide applications but also protect them with personalized security measures that are virtually impossible for unauthorized users to bypass. Modern smartphones support multiple fingerprint profiles and facial recognition settings that can be configured to provide different access levels and interface configurations based on the authentication method used. For instance, a primary fingerprint might provide access to the standard interface, while an alternate finger could unlock a hidden workspace containing concealed applications, creating a sophisticated dual-interface system that appears completely normal to casual observers. iOS devices can leverage the Shortcuts app combined with biometric authentication to create complex access workflows where specific Touch ID or Face ID authentications trigger custom shortcuts that reveal hidden applications or interface modifications. Android devices offer even more extensive biometric integration through applications like "App Hider" or "Parallel Space" that support fingerprint-protected hidden spaces and biometric app launching. Advanced implementations can include behavioral biometrics that learn user interaction patterns and provide access based on typing rhythms, swipe patterns, or device handling characteristics, creating personalized access methods that are unique to each individual user. This sophisticated approach ensures that even if someone gains physical access to the device, the hidden applications remain completely inaccessible without the specific biometric credentials, providing the highest level of concealment and security available through consumer technology.