How to Share Your Screen Without Showing Embarrassing Notifications
# How to Share Your Screen Without Showing Embarrassing Notifications: A Complete Guide to Professional Digital Privacy
In our hyperconnected world, screen sharing has become an indispensable tool for remote work, online education, and virtual collaboration. However, this technological convenience comes with a hidden vulnerability that millions of professionals face daily: the dreaded notification pop-up during important presentations or meetings. Whether it's a personal text message from your partner, a notification from a dating app, a reminder about a medical appointment, or an alert from a social media platform, these interruptions can transform a professional interaction into an embarrassing moment that undermines your credibility. The anxiety of potential notification exposure has become so prevalent that many professionals report feeling stressed before every screen share, constantly worried about what might appear on their screen. This comprehensive guide addresses this modern digital dilemma by providing you with practical, tested strategies to maintain your professional image while sharing your screen. From understanding the psychology behind notification anxiety to implementing foolproof technical solutions, we'll explore every aspect of secure screen sharing. By mastering these techniques, you'll be able to present with confidence, knowing that your personal digital life remains private while you maintain the collaborative benefits of screen sharing technology.
1. Understanding Notification Types and Their Professional Impact
Not all notifications carry the same level of embarrassment potential, and understanding the hierarchy of digital interruptions is crucial for developing an effective privacy strategy. System notifications, such as software updates or security alerts, typically pose minimal embarrassment risk but can still disrupt the flow of a presentation. Personal communication notifications from messaging apps like WhatsApp, Telegram, or iMessage represent a moderate risk category, as they might reveal personal relationships or conversations that could be misinterpreted in a professional context. High-risk notifications include those from dating applications, health-related apps, financial services, or social media platforms that might display inappropriate content or personal information. The timing of these notifications often correlates with their potential for disruption – morning notifications tend to include news updates and work-related messages, while evening notifications are more likely to contain personal or entertainment-related content. Research conducted by digital workplace consultants indicates that 73% of professionals have experienced at least one embarrassing notification during screen sharing, with 34% reporting that such incidents negatively impacted their perceived professionalism. Understanding these categories helps you prioritize which notification sources require the most stringent privacy controls and allows you to develop a risk-based approach to notification management during screen sharing sessions.
2. Pre-Meeting Preparation - Setting Up Your Digital Environment

Effective screen sharing privacy begins long before you click the "share screen" button, requiring a systematic approach to preparing your digital environment. The foundation of this preparation involves creating a dedicated "presentation mode" routine that you execute 15-30 minutes before any scheduled screen sharing session. This routine should include closing all non-essential applications, particularly social media platforms, personal messaging apps, and entertainment applications that might generate distracting notifications. Email applications require special attention – while you may need them open for work purposes, consider switching to focused inbox modes or temporarily disabling desktop notifications. Browser preparation is equally critical; close personal tabs, clear recent downloads from view, and ensure your bookmarks bar doesn't contain potentially embarrassing shortcuts. Desktop organization plays a vital role in maintaining professionalism – remove personal files, screenshots, or documents from your desktop, and consider using a clean, professional wallpaper rather than personal photos. Create a standardized folder structure for presentation materials, ensuring quick access to necessary files without exposing personal directories. Many professionals find it helpful to maintain a separate user account specifically for presentations and screen sharing, though this requires advance planning and isn't always practical for spontaneous meetings. The key is developing a consistent pre-meeting checklist that becomes second nature, reducing the cognitive load during actual presentations while ensuring comprehensive privacy protection.
3. Operating System-Specific Do Not Disturb Features

Modern operating systems provide sophisticated notification management tools, but their effectiveness depends on proper configuration and understanding of their limitations. Windows 10 and 11 offer "Focus Assist" (formerly "Quiet Hours"), which can be configured to automatically activate during specific hours, when duplicating displays, or when running full-screen applications. The priority-only mode allows critical notifications while suppressing social media and entertainment apps, though it requires careful customization of your priority contact list. macOS provides "Do Not Disturb" functionality with time-based scheduling and the ability to mirror iPhone settings, but users must understand that some system notifications may still appear even when activated. The "Screen Time" integration allows for app-specific notification scheduling, providing granular control over which applications can interrupt during specific periods. Linux distributions vary significantly in their notification management capabilities, with GNOME offering comprehensive controls through its notification settings, while other desktop environments may require third-party solutions. Mobile device integration presents additional complexity – both iOS and Android can sync Do Not Disturb settings across devices, but this synchronization isn't always reliable and may not cover all applications. Understanding the nuances of your specific operating system version is crucial, as notification behavior can change significantly between updates. Many professionals overlook the importance of testing these settings in advance, leading to surprises during actual presentations when notifications still appear despite believing they were properly configured.
4. Application-Level Notification Controls

While system-wide notification controls provide broad protection, application-level management offers the precision needed for comprehensive privacy during screen sharing. Each major application category requires specific attention and configuration strategies. Communication platforms like Slack, Microsoft Teams, and Discord offer granular notification settings that can be scheduled or toggled quickly before meetings. These applications often provide "presentation mode" or "busy" status options that automatically suppress notifications while indicating your unavailability to colleagues. Email clients present unique challenges because they're often essential for work but can receive highly personal messages. Outlook, Gmail, and Apple Mail all offer focused inbox features and VIP sender lists that can help filter important work communications from personal messages. Social media applications require the most aggressive management, as their notifications are designed to be attention-grabbing and often contain personal or potentially inappropriate content. Facebook, Instagram, Twitter, and LinkedIn all provide detailed notification customization, but their default settings prioritize engagement over privacy. Browser notifications from websites present another layer of complexity, as they can appear even when the originating website isn't actively being used. Chrome, Firefox, and Safari all allow site-specific notification blocking, but this requires proactive management of permissions. Mobile applications synchronized with desktop versions can create unexpected notification sources, requiring coordination between device settings. The key to effective application-level control is creating notification profiles that can be quickly activated before screen sharing sessions, rather than relying on permanent settings that might cause you to miss important communications during non-presentation times.
5. Third-Party Tools and Software Solutions

When built-in operating system features prove insufficient, numerous third-party solutions offer enhanced notification management and screen sharing privacy. Professional presentation software like Presenter Coach, Presentation Assistant, and CleanMyMac's Presentation Assistant provide comprehensive notification blocking specifically designed for screen sharing scenarios. These tools often include features like automatic application closing, notification suppression, and desktop cleaning with one-click activation. For Windows users, applications like Cold Turkey Blocker and FocusMe offer sophisticated scheduling and blocking capabilities that extend beyond simple notification management to include application and website blocking during presentation periods. Mac users can leverage tools like Bartender for menu bar management, HacKit for notification filtering, and Mela for comprehensive focus management. Cross-platform solutions like Freedom and RescueTime provide notification blocking alongside productivity tracking, helping users understand their notification patterns and optimize their digital habits. Virtual desktop solutions represent another approach – applications like Dexpot for Windows or the built-in Spaces feature on macOS allow users to maintain separate desktop environments for presentations and personal use. Screen recording and streaming software like OBS Studio, Camtasia, and ScreenFlow often include presentation modes that automatically manage notifications and system alerts. Cloud-based solutions are emerging that provide notification management across multiple devices and platforms, though these require careful consideration of data privacy implications. When selecting third-party tools, consider factors like resource usage, reliability, cost, and integration with existing workflows, as poorly chosen solutions can create more problems than they solve.
6. Browser-Specific Privacy Settings

Web browsers serve as gateways to countless notification sources, making browser-specific privacy configuration essential for comprehensive screen sharing security. Modern browsers have evolved sophisticated notification systems that can display alerts from websites, web applications, and browser extensions, each requiring specific management strategies. Chrome's notification system allows granular control over site permissions, with the ability to block all notifications, allow only from specific sites, or require permission for each request. The "Site Settings" menu provides comprehensive control over notification permissions, but users must actively manage these settings as new websites frequently request notification access. Firefox offers similar functionality through its "Privacy & Security" settings, with additional features like notification scheduling and the ability to clear all notification permissions simultaneously. Safari's notification management integrates with macOS system settings, providing unified control but potentially creating confusion about where specific settings are configured. Edge browser has inherited many Chrome features while adding Microsoft-specific integrations that can create additional notification sources through Office 365 and other Microsoft services. Browser extensions represent a significant source of unexpected notifications, as many productivity tools, social media managers, and utility extensions display alerts that can appear during screen sharing. Ad blockers and privacy extensions can help reduce unwanted notifications, but they may also interfere with legitimate web application functionality. The concept of "notification fatigue" has led to the development of browser features like notification grouping and smart filtering, but these features require user training to be effective. Regular browser maintenance, including clearing notification permissions and reviewing extension privileges, should be part of every professional's digital hygiene routine.
7. Mobile Device Integration and Synchronization
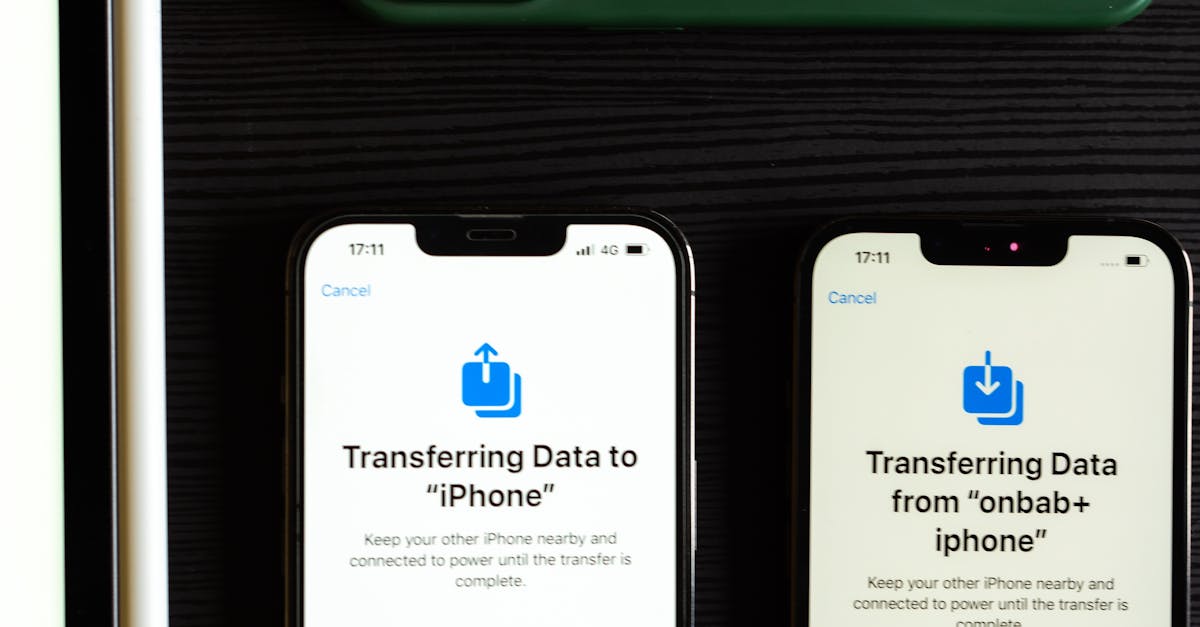
The interconnected nature of modern devices means that mobile device notifications can unexpectedly appear on desktop computers during screen sharing sessions, creating privacy risks that many users don't anticipate. Apple's ecosystem integration through iCloud and Handoff can cause iPhone notifications to appear on Mac computers, including personal messages, app alerts, and even phone calls. This synchronization can be partially controlled through System Preferences, but the settings are complex and not always intuitive. Android devices connected to Windows computers through "Your Phone" app or Chrome browser synchronization can similarly display mobile notifications on desktop systems. Google's ecosystem integration means that notifications from Android devices can appear in Chrome browsers, Gmail interfaces, and other Google services during screen sharing. The challenge with mobile integration is that these notifications often contain the most personal content – text messages, dating app alerts, health reminders, and social media interactions that are particularly embarrassing in professional contexts. Cross-device notification management requires understanding multiple synchronization pathways and their individual controls. iMessage synchronization can be managed through Apple ID settings, but this affects functionality across all devices. Google account synchronization offers granular controls through account settings, but changes can impact the convenience of cross-device workflows. Many professionals find it necessary to temporarily disable device synchronization before important presentations, though this requires advance planning and can disrupt normal workflows. The emergence of smartwatch integration adds another layer of complexity, as notifications suppressed on phones and computers may still appear on wearable devices, potentially causing distraction even if they don't appear on shared screens.
8. Creating Professional Screen Sharing Profiles
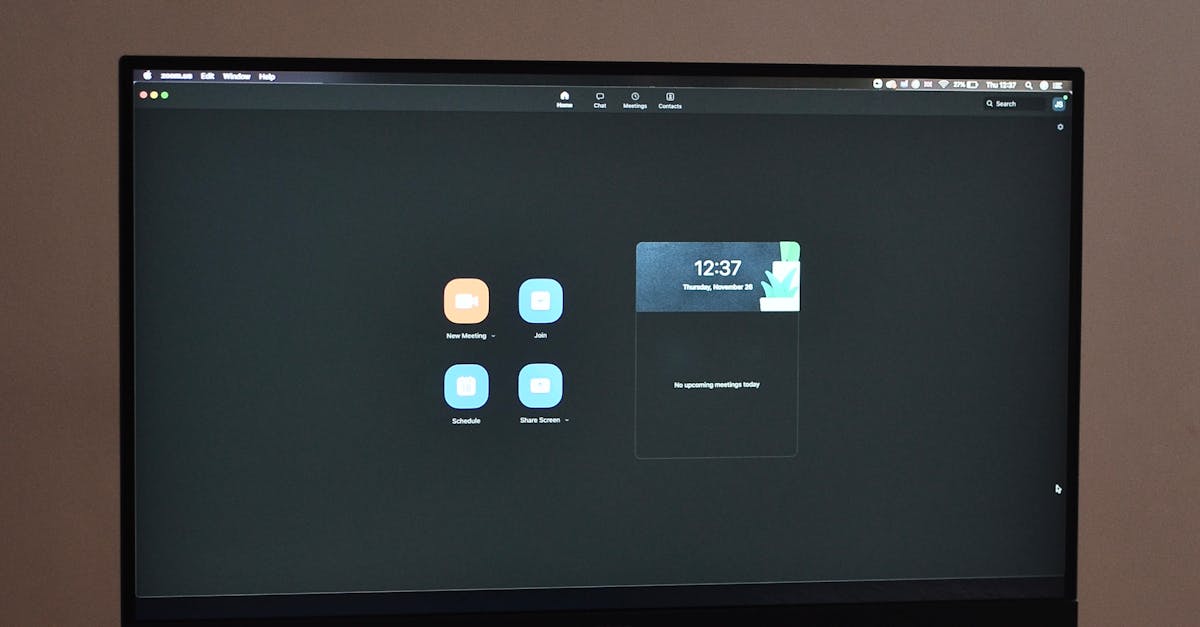
Developing dedicated profiles or user accounts specifically for screen sharing represents one of the most effective strategies for maintaining privacy during professional presentations. This approach involves creating a clean, controlled digital environment that eliminates the risk of personal notifications while maintaining access to necessary professional tools. Windows 10 and 11 support multiple user profiles with different notification settings, application installations, and desktop configurations. Creating a "presentation profile" allows you to maintain a completely separate digital identity for screen sharing, with only work-related applications installed and configured. This profile can have aggressive notification blocking, clean desktop organization, and professional wallpapers without affecting your personal computing experience. macOS offers similar functionality through user accounts and parental controls, though the setup process requires administrative privileges and advance planning. The presentation profile approach extends beyond notification management to include browser bookmarks, recent file lists, application preferences, and even different cloud service accounts. This separation ensures that no personal information can accidentally appear during screen sharing, regardless of notification settings. However, maintaining separate profiles requires discipline in switching between accounts and ensuring that necessary presentation materials are accessible from the professional profile. Cloud storage services like OneDrive, Google Drive, and Dropbox can help bridge the gap between profiles while maintaining separation of personal and professional content. Some organizations provide dedicated presentation computers or virtual machines specifically for screen sharing, eliminating personal device risks entirely. The profile approach also facilitates better security practices, as the presentation profile can have enhanced security settings and limited internet access that might be impractical for daily personal use.
9. Real-Time Monitoring and Quick Response Strategies

Even with comprehensive preparation, unexpected notifications can still appear during screen sharing sessions, making real-time monitoring and quick response strategies essential skills for professional presenters. Developing situational awareness during screen sharing involves understanding what's visible to participants and maintaining peripheral vision for potential notification alerts. Most screen sharing platforms provide presenter views that show exactly what participants can see, allowing for quick identification of privacy breaches. Learning keyboard shortcuts for rapid notification dismissal, application switching, and screen sharing controls can help minimize the impact of unexpected alerts. Windows users should master Alt+Tab for application switching, Windows+D for desktop access, and platform-specific shortcuts for ending screen sharing. Mac users need to understand Command+Tab, Mission Control gestures, and the various ways to quickly exit screen sharing modes. The psychological aspect of real-time response is equally important – maintaining composure when embarrassing notifications appear helps minimize their impact on professional credibility. Developing standard phrases or explanations for notification interruptions can help maintain presentation flow while addressing the distraction professionally. Some presenters find it helpful to acknowledge minor interruptions with humor, while others prefer to ignore them completely and continue with their presentation. Understanding your audience and presentation context helps determine the most appropriate response strategy. Technical preparation for real-time response includes having backup presentation methods available, such as pre-recorded screen captures or alternative devices, in case notification problems become unmanageable. Practice sessions with trusted colleagues can help identify potential notification sources and develop muscle memory for quick response actions.
10. Advanced Privacy Techniques and Future-Proofing

As technology continues to evolve, advanced privacy techniques and future-proofing strategies become increasingly important for maintaining professional screen sharing security. Virtualization technology offers sophisticated solutions for creating completely isolated presentation environments through virtual machines or containers. Tools like VMware, VirtualBox, or Docker can provide clean, controlled environments that are completely separate from personal computing activities. These solutions require technical expertise and system resources but offer unparalleled privacy protection. Cloud-based presentation platforms are emerging that provide remote desktop environments specifically designed for screen sharing, eliminating local device risks entirely. Services like AWS WorkSpaces, Microsoft Azure Virtual Desktop, and Google Cloud Workstations offer professional-grade presentation environments accessible from any device. Artificial intelligence and machine learning are beginning to influence notification management, with smart filtering systems that can predict and prevent embarrassing interruptions based on context and timing. Future operating systems are likely to include more sophisticated presentation modes that automatically detect screen sharing activities and adjust notification behavior accordingly. Privacy-focused operating systems and browsers designed specifically for professional use are gaining traction, offering enhanced control over personal information exposure. The integration of biometric authentication and context-aware computing may eventually provide seamless transitions between personal and professional digital modes. As remote work becomes increasingly prevalent, the demand for sophisticated privacy tools will likely drive innovation in notification management and screen sharing security. Staying informed about emerging privacy technologies and regularly updating privacy strategies will be essential for maintaining professional credibility in an increasingly connected world. The future of screen sharing privacy will likely involve more automated, intelligent systems that require less manual configuration while providing superior protection against embarrassing digital exposures.